Evolve your defenses
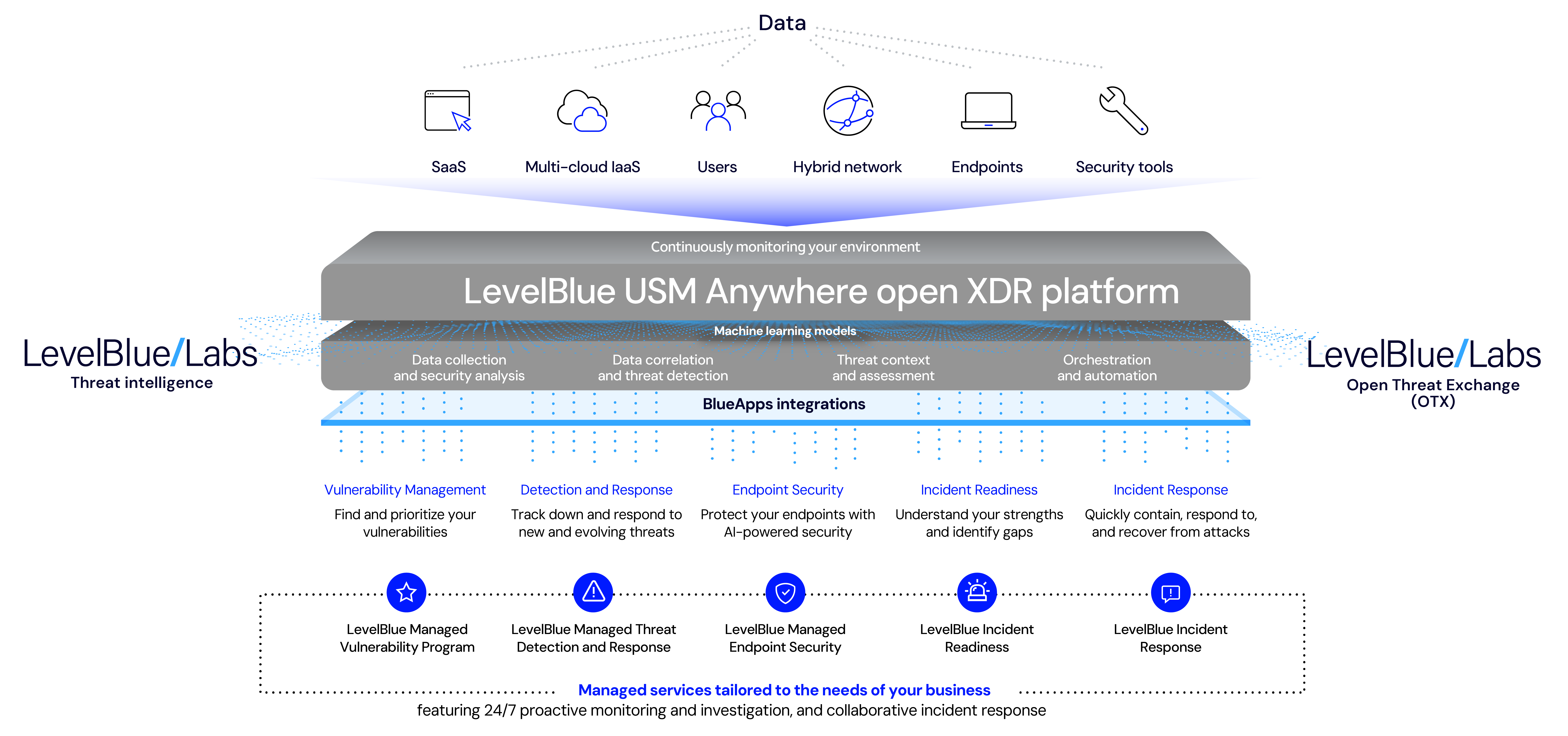
Detect and respond to threats with the LevelBlue USM Anywhere open XDR platform
Expanded data gathering
Connect the dots with better, centralized visibility and information gathering
Advanced analytics
Improve time to detect with threat intelligence that provides context and correlated insights
Automated and orchestrated workflows
Accelerate response and recovery to reduce damage and minimize downtime
Extend your security capabilities
Stay ahead of threats with better visibility, less complexity, and integrated intelligence
Enable coordinated, automated responses to threats, and streamline your workflows
Powerful third-party integrations extend our open XDR platform’s threat detection and security orchestration capabilities to a large and growing ecosystem of security and productivity tools.
Take advantage of built-in threat intelligence
Stay ahead of threats even as IT systems evolve, and adversaries change tactics. Our open XDR platform integrates curated threat intelligence from LevelBlue Labs and the Open Threat Exchange® (OTX™) powered by in-product machine learning and user and entity behavior analytics (UEBA) to predictively identify advanced threats.
Next-gen security operations in one unified platform
Extend detection and response for your customers and increase your revenue with essential security and compliance offerings powered by our open XDR platform.
Identify and disrupt advanced threats to sensitive data
Our Cybersecurity’s TDR for Government solution is designed to meet the evolving security needs of governmental entities. Built on our FedRAMP-authorized open XDR platform, it combines multiple essential security capabilities.
Enable coordinated, automated responses to threats, and streamline your workflows
Take advantage of built-in threat intelligence
Next-gen security operations in one unified platform
Identify and disrupt advanced threats to sensitive data
Discover the benefits
Adopt a holistic approach to securing your business
One centralized view
Continuously collect and analyze data from multiple sources, including endpoints, networks, cloud environments, and applications
Broad visibility and contextual insights
Enrich and correlate data from across your attack surface with expanded data gathering and advanced analytics
Fewer false positives
Eliminate noise and reduce dwell time with prioritized alerts that focus on true threats
Security orchestration, automation, and response
Make security operations more efficient and enable faster, more scalable incident response with built-in security orchestration and automation
Support for compliance
Manage security and compliance reporting using pre-built, customizable reports
Vulnerabilities uncovered
Understand where your vulnerabilities are and how to remediate them with built-in asset scanning and vulnerability assessment
Compliance
Our Cybersecurity makes compliance a top priority
FAQs
You have questions. We have answers.
What is Extended Detection and Response (XDR)?
Gartner defines XDR as follows: “Extended detection and response (XDR) delivers security incident detection and automated response capabilities for security infrastructure. XDR integrates threat intelligence and telemetry data from multiple sources with security analytics to provide contextualization and correlation of security alerts. XDR must include native sensors and can be delivered on-premises or as a SaaS offering. Typically, it is deployed by organizations with smaller security teams.”
Is XDR a replacement for EDR?
Endpoint detection and response (EDR) and XDR both help organizations detect, investigate, and respond to security incidents, but their scope and capabilities differ.
While EDR focuses on the endpoint, XDR expands its scope to multiple vectors, offering a more integrated and holistic approach to threat detection and response. This broader perspective allows for more effective threat hunting, faster incident response times, and improved overall security posture.
Is XDR better than SIEM?
In a word, yes; but XDR is really an apple, security information and event management (SIEM) more of an orange.
XDR and SIEM systems are distinct tools with different purposes and capabilities. SIEM systems aggregate and analyze log data generated across the IT environment, which can include network devices, systems, and applications. They provide real-time analysis of security alerts and also support compliance reporting and incident response. Conversely, XDR unifies control points, security infrastructure, and threat intelligence into a cohesive platform. It automatically collects and correlates data from multiple security products to facilitate threat detection and improve incident response. XDR is generally more proactive than SIEM, using machine learning and other advanced analytics to identify and respond to threats.
Will XDR identify a security incident?
XDR employs automation and machine learning to rapidly identify and respond to a security incident. Automated playbooks can execute pre-defined actions based on threat severity, reducing response time, and allowing security teams to focus on more strategic tasks. While traditional cybersecurity tools lack context—often providing isolated alerts that require manual investigation and correlation to understand the full scope of an attack—XDR provides contextual insights by analyzing data across different layers of the IT environment. This context helps security teams understand a cybercriminal’s tactics, techniques, and procedures, allowing for a more informed response.
What problems does XDR solve?
Among the challenges that XDR handles are: overcoming the complexity of emerging cybersecurity threats; providing centralized visibility into your security tools and assets for quick response; orchestrating and automating threat detection and response; and an open platform that lets you keep the security products you already have in place.
What is the difference between XDR and SOAR?
Security orchestration, automation, and response (SOAR) technology helps co-ordinate, execute, and automate tasks between various people and tools within a single platform. This allows organizations to not only quickly respond to cybersecurity attacks but also observe, understand, and prevent future incidents. In contrast, XDR offers advanced detection, rapid response, and intuitive automation without the added cost of a SOAR solution. In general, XDR offers a simpler, more intuitive solution to reduce the burden of manual work and your cybersecurity team’s time.