The perfect Rx for HIPAA compliance
Simplify and accelerate HIPAA compliance and reporting with one complete solution.
Accelerate and Simplify HIPAA Compliance Management
Any organization that transmits any health information in electronic form, including health plans, healthcare clearing houses, healthcare providers, and business associates of a covered entity, must comply with HIPAA.
Yet, according to the US Department of Health and Human Services, one of the top issues that organizations have is failure to sufficiently safeguard electronic protected health information. One of the big challenges is the number of security controls that organizations need to deploy, often requiring numerous security point products that are costly to procure and difficult to deploy and manage.
To help you achieve HIPAA compliance, including satisfying the HIPAA Security Rule, you need a HIPAA compliance software solution that is easy to deploy and monitors your critical infrastructure.
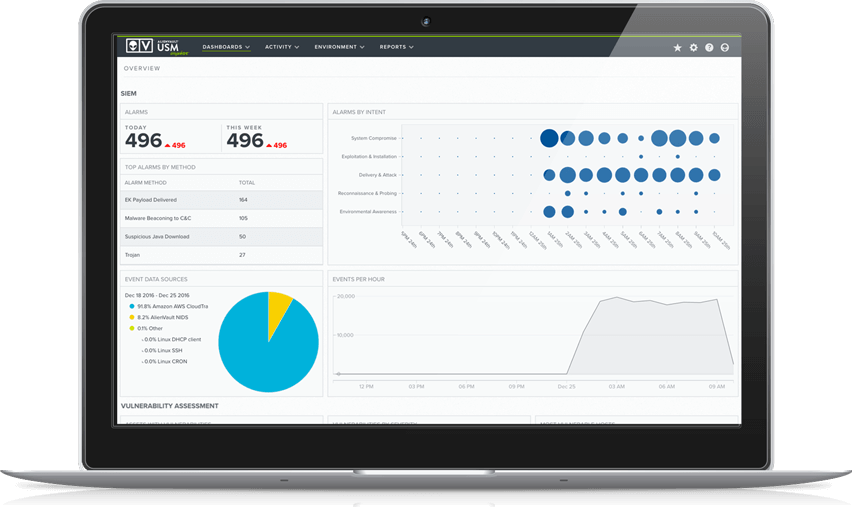
Unified Security management™ (USM) delivers a comprehensive threat detection, incident response, and HIPAA compliance management solution for your cloud and on-premises environments that costs less and delivers results in significantly less time than traditional SIEM products.
The USM platform delivers multiple security essentials to help you prepare for your next HIPAA audit faster and more easily, and in a single, unified platform:
- Discover all IP-enabled assets, including OS details, across your on-premises and cloud environments
- Identify systems with vulnerabilities, understand which assets are high-, medium-, and low risk, and identify any available patches or workarounds
- Intrusion detection detects threats, including malware and ransomware, that are active in your network with advanced, automatic correlation
- Identify both successful and failed logon attempts, and monitor user and administrator activities
- Accelerate incident response with built-in remediation guidance for every alarm, and integrated orchestrated responses that can be manually or automatically executed
- Collect events from across your on-premises and cloud environments and cloud applications for analysis, and store them for at least 12 months
- Be assured that you’re protected with continuously updated threat intelligence delivered automatically to the USM platform, including the latest correlation directives, vulnerability assessment signatures, IDS rules, guided threat responses and more
- Easily report on security controls required for HIPAA requirements with the built-in HIPAA reports, and the ability to create new custom reports and views to meet reporting requirements specific to your organization
Our Cybersecurity is trusted & verified
Our Cybersecurity makes compliance a top priority for your organization and for ours. We have adopted the NIST Cybersecurity Framework (CSF), aligning our security controls and processes with industry-proven security best practices. We use our own USM platform to demonstrate and maintain compliance, working with third-party auditors to regularly test our systems, controls, and processes.





* The ISMS that governs USM Anywhere, USM Central
Threat Detection for Healthcare Organizations
According to the Identity Theft Resource Center, healthcare organizations suffered 34.5% of breaches identified in 2016. It’s nearly impossible to stop a persistent attacker from penetrating even the most secure environment. Therefore, it’s essential to not only focus on preventing attacks, but also on detecting and responding to attacks as quickly as possible.
USM has helped healthcare organizations like Shriners Hospitals, Kaiser Permanente and Novo Nordisk accomplish these key tasks:
- Identify vulnerabilities on assets that store electronic protected health information (ePHI)
- Maintain an audit log of who has accessed ePHI, helping meet audit management requirements
- Identify systems communicating with malicious IPs, a sign of possible compromise
- Identify and respond to security incidents, including remediation advice for every alert
Comprehensive Reporting and Log Management for HIPAA Compliance
HIPAA Part § 164.312 (B) “Audit Controls” states that you must “Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.” USM is updated regularly with new compliance reports as these regulatory standards evolve, greatly reducing the time required to assess HIPAA compliance.
HIPAA Part § 164.312 (C) (2) deals with data integrity and requires that any covered organization “Implement electronic mechanisms to corroborate that electronic protected health information has not been altered or destroyed in an unauthorized manner.”
The USM platform helps entities satisfy this requirement by ingesting File Integrity Monitoring (FIM) events as well as Windows registry entries and digitally signed audit logs.
To ensure that the logs themselves have not been tampered with, the USM platform implements multiple levels of protection of your security data in transit and at rest. This ensures the integrity and confidentiality of your security data, which allows for your logs to be admissible in a court of law.

Discover How USM Supports
HIPAA Requirements
HIPAA Standard
HIPAA Requirement
Examples of How LevelBlue USM Helps
§164.308(a)(1) - Security Management Process
Implement policies and procedures to prevent, detect, contain, and correct security violations.
§164.308(a)(1)(ii)(A) - Risk Analysis
§164.308(a)(1)(ii)(D) - Information System Activity Review
- Built-in asset discovery discovers assets running on-premises, and in cloud environments (including Azure, VMware, Hyper-V, AWS).
- Identifies systems susceptible to known vulnerabilities, and ranks them as 'high', 'medium' and 'low' risk to aid prioritization.
- Identifies patches or workarounds available to vulnerable systems.
- Identifies where security tools, such as antivirus and firewalls, have been disabled or have failed to start.
- Monitors access to and attempt to modify system and application binaries, configuration files, log files.
- Monitors user and administrator activities in cloud environments such as Azure and AWS, and within cloud applications such as Office 365.
- Continuously updated threat intelligence ensures that USM is operating with the latest correlation directives, vulnerability signatures, IDS rules, reports, guided threat response and more.
- Aggregates, analyzes and archives logs and events from systems, applications and devices from across your on-premises and cloud environments.
- Identifies logon success and failures.
- Identifies privilege escalation attempts.
- Identifies unauthorized attempts to access or modify key logs.
§164.308(a)(3) - Workforce Security
Implement policies and procedures to ensure that all members of its workforce have appropriate access to electronic protected health information ..., and to prevent those workforce members who do not have access ... from obtaining access to electronic protected health information.
§164.308(a)(3)(ii)(A) - Authorization and/or Supervision
§164.308(a)(3)(ii)(C) - Termination Procedures
- Monitor access attempts to critical files and data, and alarm when unauthorized attempts are detected.
- Capture and monitor all login successes and failures to critical assets, particularly those containing electronic protected health information.
- Monitor for logon or access attempts from the accounts of users who have been de-provisioned.
§164.308(a)(4) - Information Access Management
Implement policies and procedures to prevent, detect, contain, and correct security violations.
§164.308(a)(4)(ii)(C) - Access Establishment and Modification
- Captures all user account creation and modification activities.
- Identifies logon success and failures.
- Identifies privilege escalation attempts.
§164.308(a)(5) - Security Awareness and Training
Procedures for monitoring log-in attempts and reporting discrepancies
§164.308(a)(5)(ii)(A) - Security Reminders
§164.308(a)(5)(ii)(B) - Protection from Malicious Software
§164.308(a)(5)(ii)(C) - Log-in Monitoring
§164.308(a)(5)(ii)(D) - Password Management
- Provision for automated updates of USM infrastructure whenever updates are made available.
- Continuously updated threat intelligence ensures that USM is operating with the latest correlation directives, vulnerability signatures, IDS rules, reports, guided threat response and more.
- Identifies systems susceptible to known vulnerabilities, or that may not have antivirus installed and/or operational.
- Identifies indicators of malware-based compromise, and enables orchestrated responses that can be automated or manually invoked to isolate infected systems and block malicious domains.
- Monitors and stores events from antivirus solutions that could indicate a compromise, or attempt to disable antivirus software.
- Monitors for changes to Office 365 policies including Information Management, and more.
- Continuously updated threat intelligence ensures that USM is operating with the latest correlation directives, vulnerability signatures, IDS rules, reports, guided threat response and more.
- Captures and enables monitoring of logon success and failures to systems, security devices, cloud environments, and more.
- Identifies where new user and administrator accounts are created and deleted.
- Monitors public and dark web sources for the trade or communication of stolen credentials.
- Identifies use of default system accounts on Windows machines.
- File Integrity Monitoring can detect changes and access to critical system and application files, and Windows Registry entries.
§1164.308(a)(6) - Security Incident Procedures
Implement policies and procedures to prevent, detect, contain, and correct security violations.
§164.308(a)(6)(ii) - Response and Reporting
- Correlates events to detects threats
- Generates alarms on threats, classifying them across a kill-chain taxonomy to inform the risk level of that threat.
- Enables threat investigation and provides context to determine the nature of the threat.
- Provides recommended incident response guidance to contain or remediate the threat.
- Enables labels to be applied to alarms.
- Security orchestration and response capabilities enable manual or automated incident response, driving actions with leading security and IT operations tools including Cisco Umbrella, Carbon Black, Palo Alto Firewalls, and more.
- Enables creation of incident tickets within popular solutions like ServiceNow, directly from within the USM Anywhere console.
- Continuously updated threat intelligence ensures that USM is operating with the latest correlation directives, vulnerability signatures, IDS rules, reports, guided threat response and more.
§164.308(a)(7) - Contingency Plan
Establish (and implement as needed) policies and procedures for responding to an emergency or other occurrence (for example, fire, vandalism, system failure, and natural disaster) that damages systems that contain electronic protected health information.
§164.308(a)(7)(ii)(E) - Applications and Data Criticality Analysis
- USM Anywhere provides a fault resilient architecture that assures durability of all captured event and log data from your environments.
§164.312(a) - Access Control
Implement technical policies and procedures for electronic information systems that maintain electronic protected health information to allow access only to those persons or software programs that have been granted access rights.
§164.312(a)(2)(iii) - Automated Logoff
§164.312(a)(2)(iv) - Encryption and Decryption
- Monitors for changes to Windows Group Policy and Office 365 policies that define automated logoff, session timeout, and access token timeout parameters.
- Monitors for changes to Windows Registry or application configuration files that define encryption settings for protected health information.
§164.312(b) - Audit Controls
Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
- Monitors for changes to Office 365 policies including Data Leakage Protection (DLP), information management, and more.
- File Integrity Monitoring can detect modification attempts to applications or online storage containing electronic protected health information.
- Unified log collection, review and analysis, with triggered alarms for high risk systems.
§164.312(c)(1) - Integrity
Implement policies and procedures to protect electronic protected health information from improper alteration or destruction.
§164.312(c)(2) - Audit Controls
- Monitors for changes to Office 365 policies including Data Leakage Protection (DLP), information management, and more.
- File Integrity Monitoring can detect modification attempts to applications or online storage containing electronic protected health information.
§164.312(e)(1) - Transmission Security
Implement technical security measures to guard against unauthorized access to electronic protected health information that is being transmitted over an electronic communications network.
§164.312(e)(2)(i) - Integrity Controls
§164.312(e)(2)(ii) - Encryption
- Discover unauthorized communications, such as between untrusted networks and systems within the cardholder data environment.
- Monitors for changes to Office 365 policies including Data Leakage Protection (DLP), information management, and more.
- File Integrity Monitoring can detect modification attempts to applications or online storage containing electronic protected health information.
- Monitors for changes to Windows Group Policy and Office 365 policies that define automated logoff, session timeout, and access token timeout parameters.
- Monitors for changes to Windows Registry or application configuration files that define encryption settings for protected health information.