Accelerate detection and response
Get access to the expertise and insights you need to secure your business 24/7
Shoulder-to-shoulder support
Bridge your skills gap with seasoned experts
Broad visibility into threats
Get help managing a large, diverse attack surface
Strengthened security posture
Stay ahead of emerging threats with advanced controls
MDR from the experts
Let our team help protect your organization in real time
Rapid detection and response
Proactively monitor and manage threats across your attack surface
Attackers don’t rest. Neither do we.
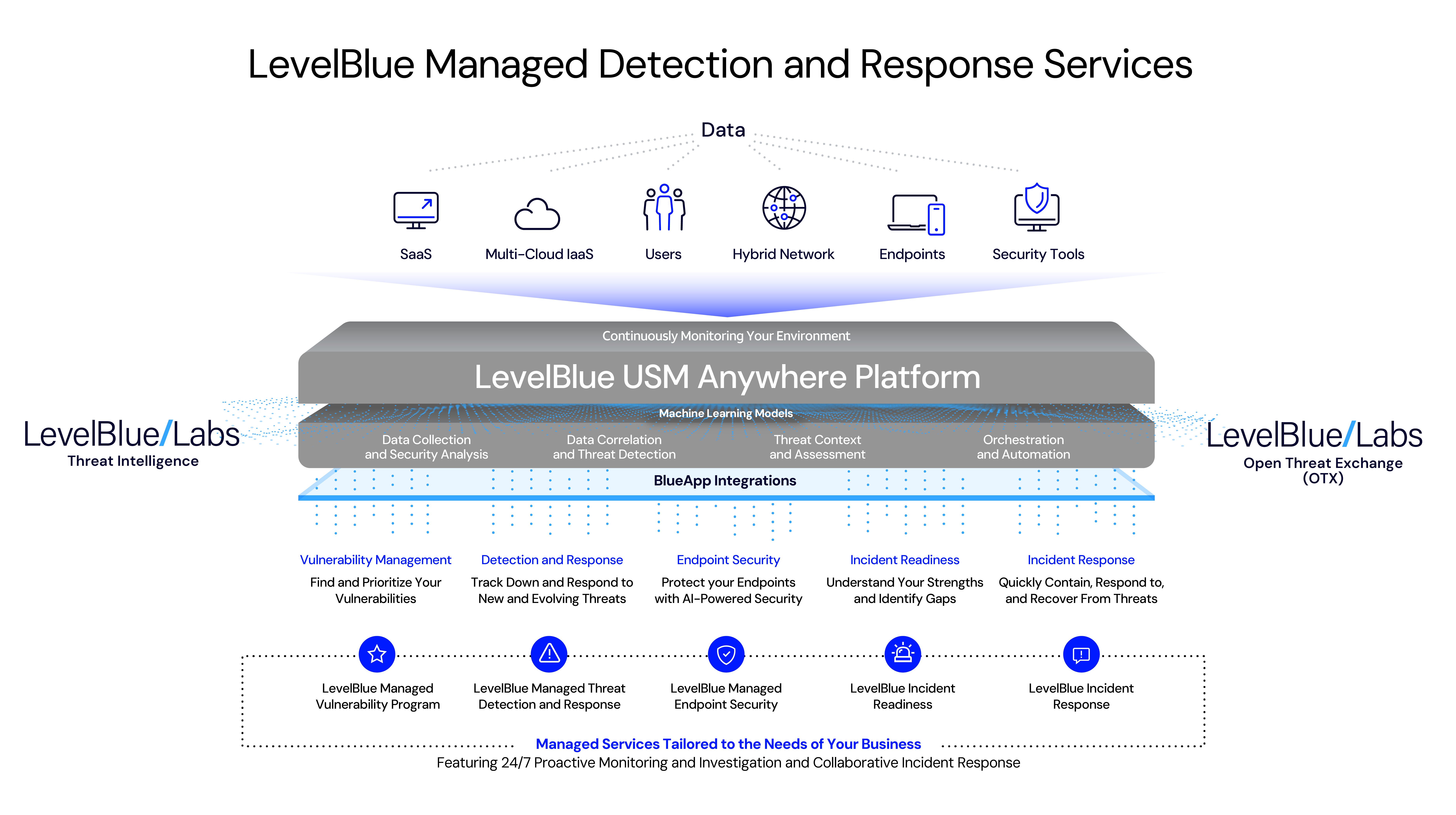
With Managed Threat Detection and Response from LevelBlue, our elite team of cybersecurity professionals uses one centralized dashboard to track down and manage threats across your business.
Secure highly regulated data
A 24/7 managed service designed to protect sensitive data
Mitigate risk and improve resiliency with LevelBlue Managed Threat Detection and Response, a 24/7 service built on our FedRAMP Moderate-authorized open XDR platform and managed by an experienced, US-based team.
Secured endpoints
Get AI-driven responses to threats on the endpoint
The endpoint remains a top attack vector, but organizations are finding it tough to manage and secure the growing number of traditional and non- traditional endpoint devices.
With LevelBlue’s Managed Endpoint Security with SentinelOne, one team keeps watch across your diverse and distributed attack surface—and in one holistic view, so your endpoint threats can be found and addressed in real time.
Vulnerability management
Uncover your biggest risks
As your IT landscape evolves, system flaws, configuration errors, and other issues can create new vulnerabilities attackers might use to exploit security weaknesses.
The LevelBlue Managed Vulnerability Program combines our consultants’ expertise with a portfolio of industry-leading vulnerability management solutions to help you manage your risk.
Incident readiness
Be ready for your worst-case scenario
In today’s threat landscape, it’s not if an attack will occur, but when. To be operationally resilient, you need to be proactive about understanding your strengths and identifying areas for improvement in your security infrastructure.
Our incident readiness services help you strategically plan for a security event.
Incident response
Have a plan for when things don’t go as planned
What happens when your business is attacked? You need to be able to respond quickly and effectively to minimize the damage.
LevelBlue offers robust incident response services that are custom-built for your organization and a team of skilled IR and forensic specialists to assist when things go wrong.
Proactively monitor and manage threats across your attack surface
A 24/7 managed service designed to protect sensitive data
Get AI-driven responses to threats on the endpoint
Uncover your biggest risks
Be ready for your worst-case scenario
Have a plan for when things don’t go as planned
Discover the benefits
Get dedicated support from a team that understands your cyber risks and priorities
Global expertise
Overcome gaps in skill and experience and reduce the burden on your staff with our elite team of experienced cybersecurity professionals
Continuous monitoring
Secure your business with proactive security monitoring and threat hunting with analysts using state-of-the-art tools and threat intelligence
Increased efficiencies
Streamline security operations with an open XDR platform that includes powerful integrations, orchestrated response actions, simplified workflows, and more
Curated intelligence
Stay ahead of emerging threats with the latest intelligence and correlated rules powered by machine learning
FAQs
You have questions. We have answers.
What is managed detection and response?
Managed detection and response (MDR) can provide faster, less-complex deployment across your environment, helping to reduce the costs associated with managing a security technology stack and the challenges of recruiting and retaining skilled cybersecurity experts
How does MDR differ from traditional cybersecurity tactics?
MDR provides organizations with experts who monitor their endpoints, networks, and cloud environments, and respond to threats at any time. Compared to other tactics, MDR delivers several improvements including: threat management that is both reactive and proactive; broad access to skilled cybersecurity experts; reduced mean times to both detection and response; effective resource augmentation with specialized skills such as threat hunting and forensic investigation; and guided response and remediation to restore endpoints in the event of an established threat.
Can MDR services be integrated with our existing cybersecurity infrastructure?
Yes. Integration includes initial provisioning, configuration, and tuning of the LevelBlue Unified Security Management (USM) Anywhere platform; staff training; development of a custom incident response plan, and an optional threat modeling workshop.
What role do AI and machine learning play in MDR?
Machine learning helps optimize security operations by making threat detection and response faster and more accurate. By using machine learning, tools automate and improve the analysis of large amounts of event and incident data from multiple sources in near real time. They identify patterns and anomalies in the data and then prioritize alerts for suspected threats or critical vulnerabilities that need patching. Analysts use this real-time intelligence to enhance their insights and understand where they can scale their responses, or where there are time-sensitive detections they need to investigate. Machine learning can also augment traditional threat detection methods, such as signature-based tools that alert on known bad traffic. By combining predictive analytics that alert based on behavioral anomalies with existing knowledge about bad traffic, machine learning helps to reduce false positives. It also helps make security operations more efficient by automating workflows for more routine security operations response.
Are MDR solutions customizable for different business sizes and types?
MDR is highly adaptive to your specific business landscape and sector. Your outsourced cybersecurity experts can, for example, create bespoke response playbooks and triage plans, and work with your internal team to define processes and workflows.
What are key features to look for in an MDR service?
Many MDR solutions offer consumers similar-seeming features, so it’s important to understand exactly what is included in the service. When selecting an MDR, consider the following:
- Staffing—Do you have anyone internal that will assist with response, or do you need an MDR service that handles everything?
- SOC staffing—Some MDR offerings included dedicated Tier 1 analysts. Be sure to understand what kind of staffing comes with your MDR choice.
- The MDR’s visibility—A SIEM or other monitoring tool alone doesn’t provide complete visibility into threat actions. Ask about the solutions the offering is based on and review the threat visibility provided by the offering.
- Detection Capabilities—Your MDR provider’s detection capabilities need to be based on continually updated threat intelligence.
How are incident responses managed in MDR?
When something suspicious is identified on your network, the MDR team immediately goes to work, isolating the threat so it can’t spread to other parts of your network infrastructure. After containment, the team sets to work analyzing it to fully understand its nature. We also work with you on remediation to validate the threat has been eradicated and verifying it hasn’t returned. The final part of the incident response is a deep investigation into the root cause of the incident, with the goal of creating customized rules and workflows that harden your posture.
What should businesses consider before implementing an MDR solution?
Resources and expertise are two key factors in making any cybersecurity purchasing decision. Our MDR solution employs highly trained experts around the world and collaborates with the leading cybersecurity technology suppliers to create a service that can provide extensive, highly advanced detection, remediation, and analysis at any scale.