Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
Executive Summary
While freeware does not have monetary cost, it may come at a price. There may be limitations to freeware such as infrequent updates, limited support and hidden malicious software. Some freeware programs may have added software packages that can include malicious software such as trojans, spyware, or adware. It’s important to have additional layers of defense to provide that your environment is protected.
The Managed Threat Detection and Response (MTDR) analyst team was notified of malware on a customer’s assets who frequently uses freeware. The primary piece of malware that was detected by Cisco® Secure Endpoint (formerly AMP for Endpoints) did not appear to be particularly malicious, so the investigation was originally reported as a medium severity. After some time, several alarms were raised due to additional malware that was encountered on multiple assets within the customer’s environment and it was determined they were likely caused by freeware. After some investigating, a report was created by the analyst containing a list of infected machines, files, and their related malware families. The severity of the investigation was changed to a high severity, and the customer was notified based on their incident response plan (IRP) to begin immediate remediation efforts.
Investigation
Initial Alarm Review
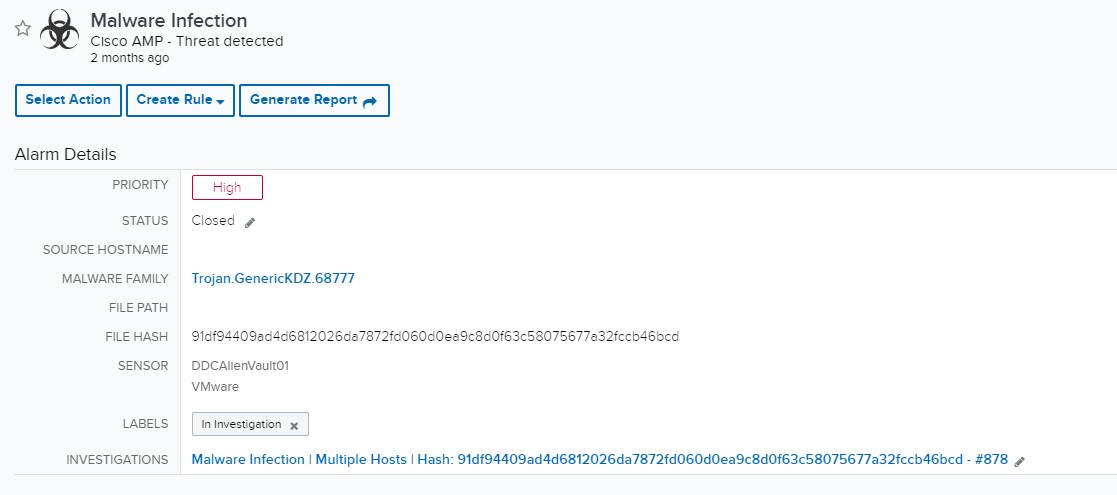
Malware Infection
Cisco Secure Endpoint – Threat detected
The Initial alarm was raised due to a piece of malware detected by Cisco® Secure Endpoint that was indicative of a single malware infection. The first detection that emerged appeared to be benign, as it was reported by multiple open source intelligence (OSINT) sites as known-clean files. Due to the detection of this original file, this investigation was set at a medium severity as a precautionary measure.
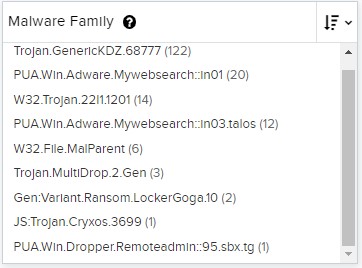
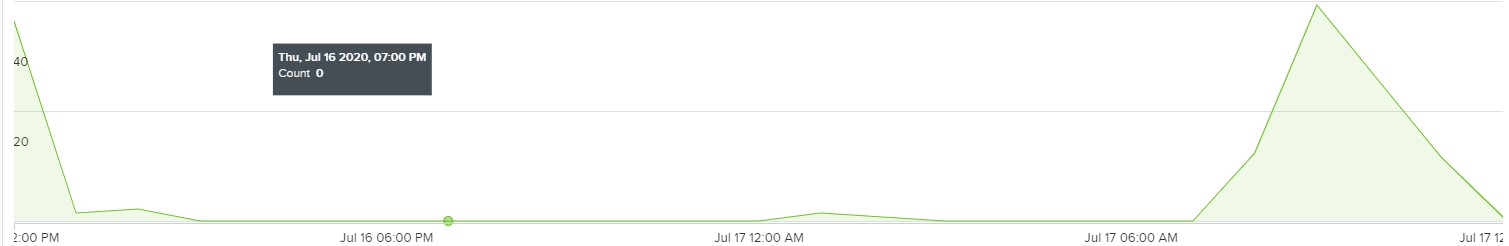
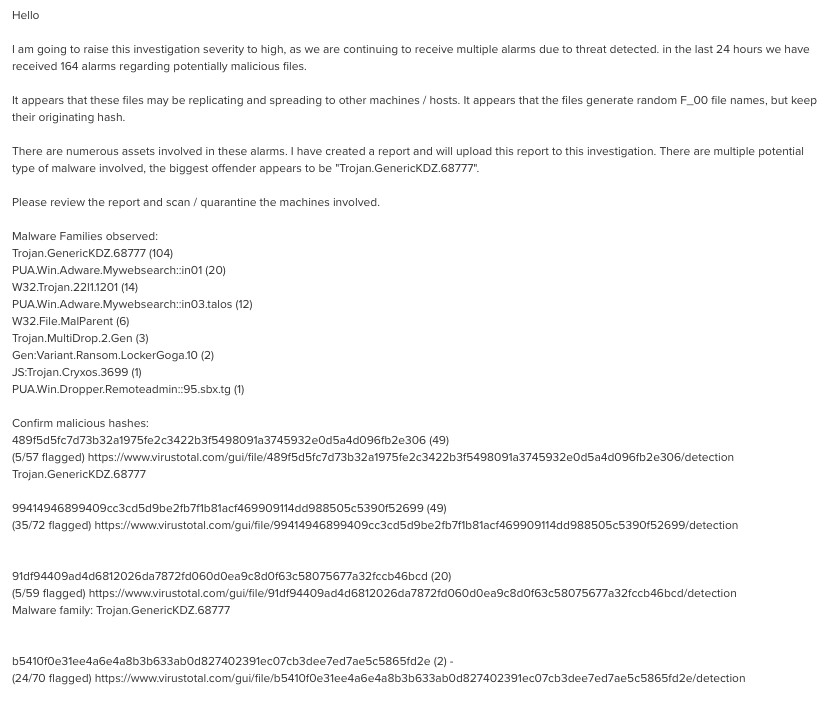
After some time, additional alarms were raised that were indicative of a deeper, more malicious infection. It became clear that additional investigation was necessary. During the investigation, nearly two hundred events of varying malware infections were detected, indicating there was propagating malware.
The detected events of malware were filtered for benign hashes using the AT&T Alien Labs Open Threat Exchange (OTX) as well as other OSINT sites. The malicious files were organized into a report with infected files, hashes, as well as a list of the fifty suspected infected assets. After the report was organized and the additional alarms were posted within the investigation, the severity was increased from medium to high to prompt immediate customer response and quarantine of these threats.
Expanded Investigation
Suspected Root Cause
These alarms are rather common for this customer as they attempt to use many pieces of freeware, which are likely already infected with Trojans, adware and more. Upon further use of OSINT sites, the file that appears to have been propagating across the customer’s network was linked to an interactive advertising company. This company has created over a hundred different toolbars, and these toolbars typically include an optional install of other freeware, which will download if you are not careful. This propagating malware was suspected to have been caused by one of the toolbars.
Customer Interaction
Customer Response(s)
After the investigation was updated, the customer was provided a report and was contacted per their Incident Response Plan (IRP). The customer contacted their team to start working through the infected machines to remove the indicated malicious files. If it was not for the organized layout of the USM platform, this malware infection could’ve been far worse.