Intelligent threat management
Combine powerful integrated security technologies and emerging threat intelligence from AlienVault Labs for unparalleled threat management and incident response.
Accelerated Incident Response and Threat Management
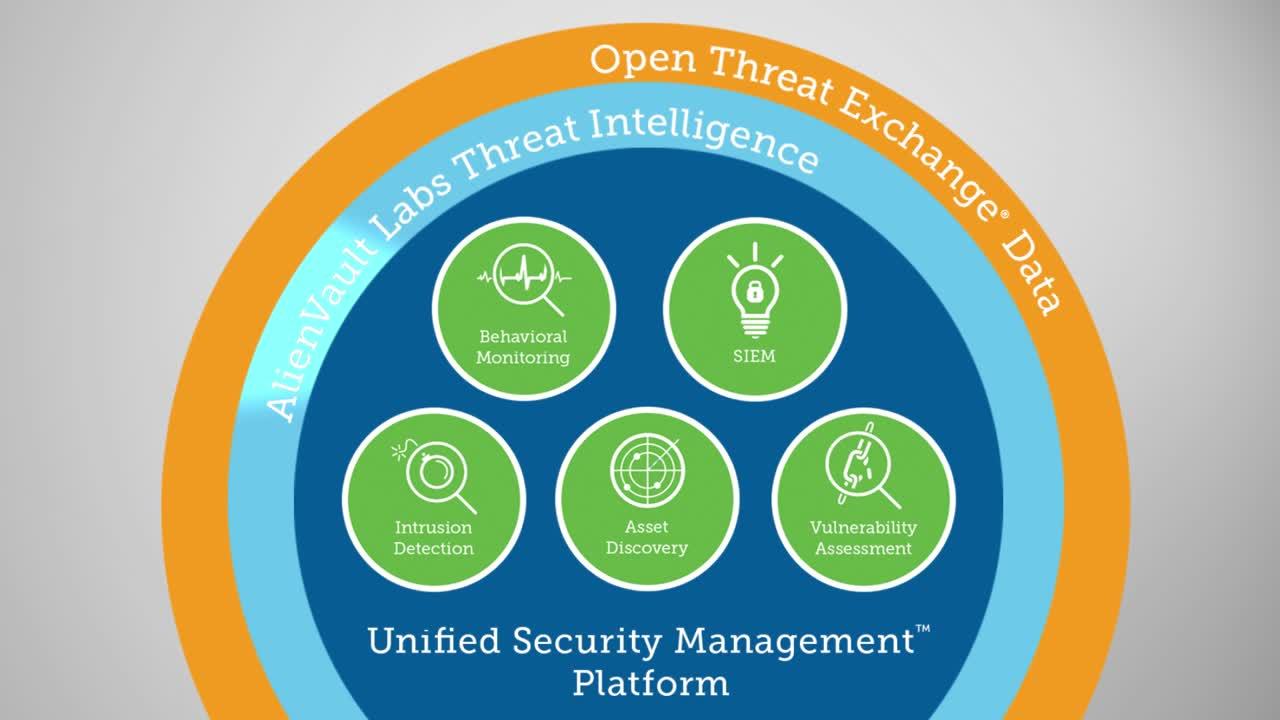
AlienVault Unified Security Management™ (USM) helps you achieve coordinated threat detection, incident response and threat management with built-in essential security capabilities, integrated threat intelligence from AlienVault Labs, and seamless workflow for rapid remediation. Consolidating threat detection capabilities like network IDS and host IDS with granular asset information, continuous vulnerability assessment, and behavioral monitoring provides you with the complete view you need for effective response.
With AlienVault USM for incident response and threat management, you can quickly:
- Identify, isolate, and investigate indicators of compromise (IOCs) before damage can occur
- Correlate security events with built-in vulnerability scan data and AlienVault Labs Threat Intelligence to prioritize response efforts
- Gain essential insight into attackers’ intent as well as techniques
- Respond to emerging threats with detailed, context-specific “how to” guidance for each alert
- Validate that existing security controls are functioning as expected
- Demonstrate to auditors and management that your incident response program is robust and reliable
Visualize and Map Threats
With the constantly evolving nature of most threats, it can be difficult to address every incident and alert that occurs in your environment. Effective incident response requires successful threat management and prioritization. However, standard methods of prioritization are very time consuming and flawed.
AlienVault USM uses a Kill Chain Taxonomy to make threat management and prioritization easy. The Kill Chain Taxonomy approach allows you to focus your attention on the most important threats by breaking attacks out into five threat categories, from highest to lowest. This shows you attack intent and threat severity, and provides you with the detailed contextual threat information you need to help you understand how they're interacting with your network.
- System Compromise – Behavior indicating a compromised system.
- Exploitation & Installation – Behavior indicating a successful exploit of a vulnerability or backdoor/RAT being installed on a system.
- Delivery & Attack – Behavior indicating an attempted delivery of an exploit.
- Reconnaissance & Probing – Behavior indicating a bad actor attempting to discover information about your network.
- Environmental Awareness – Behavior indicating policy violations, vulnerable software, or suspicious communications.