Threat detection and response for manufacturing
Unified Security Management™ (USM™) delivers enhanced security for manufacturing data.
Manufacturers use new technologies more than ever.
Today’s tech helps them simplify complex challenges, streamline the supply chain, deal with workforce shortages, compete effectively in the marketplace, and more.
Today’s technology, however, has its own challenges: cybersecurity. Manufacturers are scrambling to make sure their cybersecurity is up to speed.
The challenge
Helping to defend your data
The flow of sensitive data to effectively produce goods and meet customer demands is critical to the manufacturing industry. You have to protect proprietary designs, formulas, facility layouts, customer data, and more. A breach to any one of these areas can be crippling to the business and ripple into the market. It could affect countless partners, customers, and consumers.
From small, independent manufacturers to multi-location global operations, businesses of all sizes can be vulnerable and all may be willing to pay a hacker’s ransom to regain control of their data, devices, and applications. But business leaders are learning that the best approach is to take preventative measures to safeguard the business. They want edge-to-edge security.
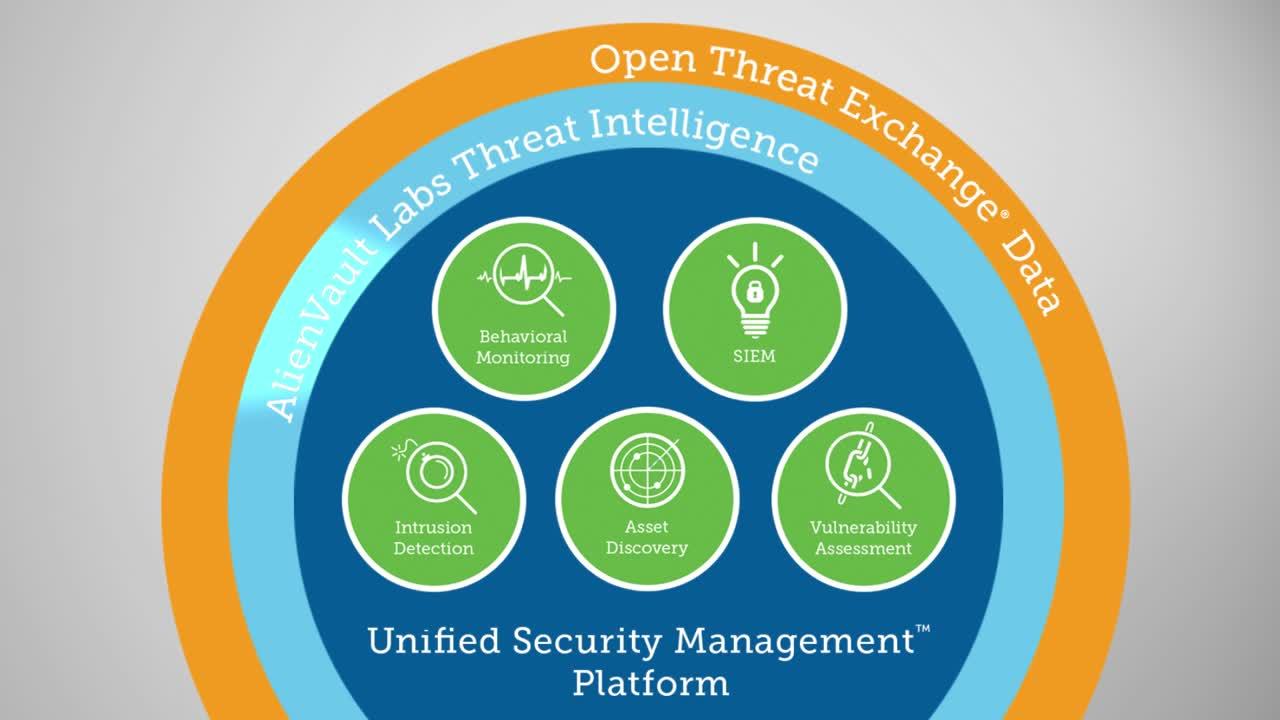
Unified Security Management™ (USM™) delivers a unified approach to help protect manufacturers’ network and data assets. It helps IT teams of all sizes—including those with limited cybersecurity resources—to assess the state of their data security. It also allows IT teams to address inefficient manual monitoring processes, the lack of security controls, and spotty threat intelligence.
Through USM, you have access to the essential capabilities you need to help address data vulnerabilities and better protect your business and customers:
Essential security controls
- Eliminate the need for additional staff to deploy, configure, and maintain separate security controls through built-in security controls
- Configure and manage all security controls through a single console
Continuous monitoring and analytics
- Correlate and analyze security events automatically
- Eliminate the need for manual monitoring and analysis
Built-in threat intelligence and response guidance
- Deliver continuous threat research and updates to security controls
- Improve incident response processes through the response guidance included in every alarm
Essential security controls
The first step for your organization? You need to understand your vulnerabilities. From there, you can implement a strategy to gain better visibility of network activity and deploy additional security controls. Although IT teams often lack the budget or staff to deploy, configure, and maintain the diverse controls they need, a multi-layered approach with professional consulting can help to address this gap.
USM’s focus on ease-of-use and deployment makes it the right fit for those manufacturers with a limited budget and few in-house resources.
USM builds in 5 essential security technologies into the USM platform, all configured and managed from a single console:
- Asset Discovery
- Vulnerability Assessment
- Intrusion Detection
- Behavioral Monitoring
- SIEM (Security Information and Event Management)
Continuous monitoring and analytics
Effectively monitoring network activity to detect malicious content and behavior is another essential aspect of manufacturing data security. Yet, many companies lack the resources to effectively achieve this and analyze the results.
One obstacle is simply volume of data. This includes event data, generated in real-time by the Internet of Things, devices, and applications across the network. Manual analysis of the gigabytes of log data for Indicators of Compromise (IoCs) is virtually impossible. Still, many IT teams in manufacturing have no other way to link events from across the network.
Logs include critical information such as user behavior, data access, system performance, as well as evidence of system compromise and data exfiltration. However, these can vary from system to system or even from version to version on the same system. They are difficult to interpret and are static, fixed points in time, without the full context or sequence of related events.
The USM platform helps to solve these problems with its automatic, continuous monitoring and analysis. Its powerful correlation engine is able to link seemingly unrelated events from across your network and tell you what are the most significant threats in your network right now.
The USM platform contains thousands of pre-built correlation directives that continuously analyze event data to identify potential security threats in your network. USM automatically detects and links behavior patterns found in disparate yet related events generated across different types of assets, putting the critical information you need at your fingertips.