PCI DSS log management & monitoring
Simplify PCI Log Management and Monitoring Across Your Environments to Reach PCI DSS Requirement 10 Faster
Accelerate Compliance in PCI DSS Requirement 10
The Payment Card Industry Data Security Standard (PCI DSS) ensures protection for credit cardholders against securities fraud. Depending on where your business is in the payment stream, PCI DSS and all of the changing security accommodations that come with it can be a lot to stay on top of every year. If you are trying to achieve PCI DSS compliance and staring at Requirement 10, wondering what to do, you’re not alone. This requirement presents some of the biggest challenges to organizations who are trying to become PCI compliant. According to Verizon, more than 90% of companies who have been breached fail to meet the requirements in this section.
However, Requirement 10 shouldn’t derail your compliance goals. You simply need a way to collect, analyze, store, and report on the “who, what, where, and when” of users who access sensitive data in your Cardholder Data Environment (CDE).
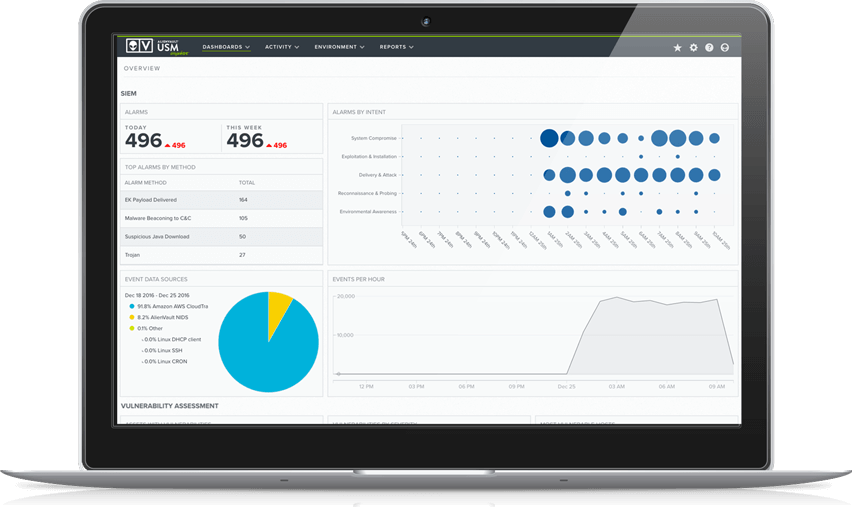
AlienVault® Unified Security Management™ (USM) delivers PCI log management capabilities and much more as a unified security monitoring and compliance management solution. AlienVault USM is affordable, easy to use, and fast to deploy, so you can accelerate compliance for your on-premises, cloud, and hybrid environments—even for the most challenging PCI requirements.
AlienVault USM delivers robust PCI log management and monitoring capabilities as part of a unified security monitoring and compliance management solution. With USM, you can readily –
Identify Your PCI Log Data Sources
- Automatically discover & inventory assets
- Create PCI asset groups to tailor your internal vulnerability scans and reports
Analyze Log Data in Incident Investigations
- Collect & analyze logs from critical network and cloud infrastructure
- Secure raw logs according to PCI requirements
Correlate Log Data with the Latest AlienVault Threat Intelligence
- Apply real-world threat context to your PCI compliance logging
- Receive continuous threat intelligence updates from the AlienVault Labs Security Research Team
Our Cybersecurity is trusted & verified
Our Cybersecurity makes compliance a top priority for your organization and for ours. We have adopted the NIST Cybersecurity Framework (CSF), aligning our security controls and processes with industry-proven security best practices. We use our own USM platform to demonstrate and maintain compliance, working with third-party auditors to regularly test our systems, controls, and processes.





* The ISMS that governs USM Anywhere, USM Central
Why PCI Requirement 10 Is Important to Your Security Posture
Even if your organization was not required to be PCI compliant, PCI DSS Requirement 10 is an important security monitoring best practice. Log management and monitoring is essential to understand what’s happening in your environment.
Furthermore, when a breach does occur, your raw log data is your paper trail of all the activities that led to the breach, giving you the forensic data you need to determine the root cause of the breach and to take corrective actions to prevent another. It’s important (and mandated in Requirement 10) to securely store raw log data for a one-year minimum.
Requirement 10 requires you to know who was logged into a system at any given point in time, what they did on the system, and how they accessed it through continuous log monitoring. However, if you have more than a handful of systems in your environment that generate log data, it’s not practical to monitor those logs individually. Instead, you need a way to collect, normalize, and analyze log data from all your critical cloud and on-premises infrastructure.
One of AlienVault USM’s core capabilities is its ability to collect and analyze event log data from its built-in detection capabilities, as well as logs from other devices in your environment. AlienVault USM monitors and correlates the log data against the latest threat intelligence, alerting you to any threats facing your environment.
Identify Your PCI-Related Log Data Sources
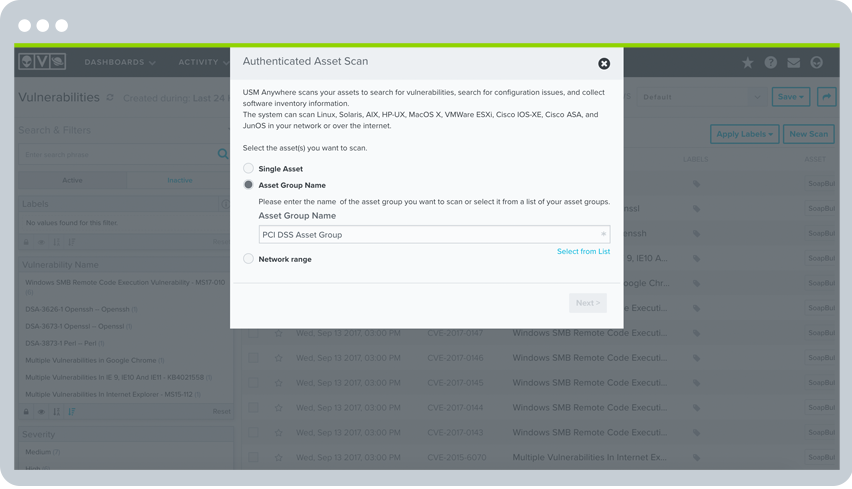
Once you’ve defined the boundaries of your cardholder data environment (CDE), the next step towards realizing PCI logging requirements is to find and identify the critical assets from which you want to collect event logs. You need to ask, “which assets process, store, or in any way ‘touch’ cardholder data?” You also need to import log data from the network infrastructure devices that provide and control access to these devices.
If you're not sure which devices are within the scope of your PCI audit, an automated asset discovery scan is a good place to start. AlienVault USM includes built-in asset discovery and inventory that scans your environments to identify all the IP-enabled devices that are online, as well as the running services on those systems and any known vulnerabilities associated with them. In addition, you can create asset groups to identify which assets are within scope of your PCI audit and run vulnerability scans on those specific groups.
Analyze Log Data in Incident Investigations
One of the main use cases for log monitoring is to support incident investigations and response activities. It's easy to understand why. Any access to cardholder data that results in a security breach will require an in-depth forensic analysis follow-up in addition to remediation of the exposures that led to the breach. In addition, it should be easy to search based on any variable to track down root causes of potential threats and exposures.
USM performs log collection from your critical applications, systems, and devices, both in your on-premises and cloud environments. The data is parsed, normalized, and immediately available as events to search on and run reports to analyze what individual users are doing across your infrastructure. Event data is connected to information about your assets, vulnerabilities, and the latest threat intelligence, giving you all the information you need in a single pane of glass to investigate an incident and respond quickly.
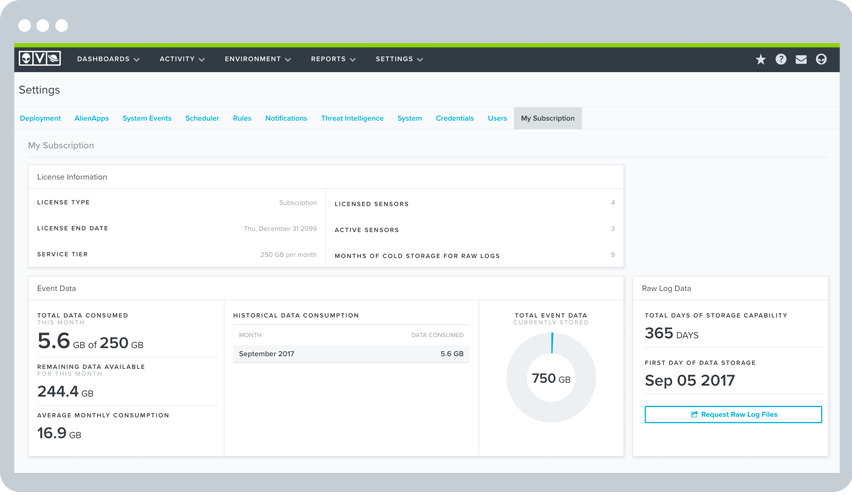
For any IT security incident or forensic investigation, it's critical to ensure that the raw log data is aggregated and stored securely and has not been altered in any way. In fact, Requirement 10.7 requires you to keep audit history for at least one year, with a minimum of three months immediately available for analysis.
The LevelBlue USM platform helps you maintain the integrity of your long-term log storage. In addition, it includes long-term data storage for the life of the active USM Anywhere subscription. Logs are stored with a write once, read many (WORM) method, making them tamper-proof. And because the AlienVault USM platform is certified compliant for PCI DSS, you can be assured of secure log monitoring and storage in the AlienVault Secure Cloud.
Correlate Log Data with Threat Intelligence
Another key aspect of Requirement 10 is to review logs on a daily basis (10.6.1). In fact, the standard specifically requires this daily log review for all systems that perform security functions, including IDS, firewalls, and authentication services. Yet, doing a manual daily log review of all your critical systems would be extremely tedious and would leave you without any time to do actual work. Besides, without security context, it’s not apparent which events are significant or how multiple, disparate events are related to each other.
This is where the automated SIEM event correlation capabilities of AlienVault USM deliver tremendous value.
In addition to providing essential security functions like intrusion detection (IDS) and vulnerability assessment, the AlienVault USM platform receives continuous threat intelligence updates from the AlienVault Labs Security Research Team. These updates help you to stay in continuous compliance, ensuring that the USM platform has the ability to detect new and updated threats through the latest correlation rules.
The AlienVault Labs Security Research Team tracks millions of malicious URLs, attacker techniques, tools, and profiles and uses this data to continuously deliver threat intelligence updates directly and automatically to the USM platform. This team leverages threat data shared by the global cybersecurity community on the AlienVault Open Threat Exchange® (OTX™), so your monitoring of logs and events to detect threats and anomalies stays up to speed with the ever-evolving global threat landscape.
This alleviates the burden of having to conduct your own threat research and then comparing that to your log data to identify threats. Instead, you get seamless, actionable threat intelligence that you can use to maintain effortless, continuous compliance.

Discover How AlienVault USM Supports
PCI DSS Requirements
PCI Requirement
PCI Sections LevelBlue USM Addresses
How LevelBlue USM Helps
1. Install and maintain a firewall configuration to protect cardholder data.
1.1, 1.2, 1.3
- Built-in asset discovery provides a dynamically updated inventory of assets across your cardholder data environment, ensuring only authorized endpoints are deployed.
- Capture events relating to configuration changes on firewalls and routers, including when user accounts get updated.
- Discover unauthorized communications, such as between untrusted networks and systems within the cardholder data environment.
2. Do not use vendor-supplied defaults for system password and other security parameters.
2.1, 2.2, 2.3, 2.4, 2.6
- Identify use of default system accounts on Windows machines.
- Non-customizable File Integrity Monitoring can detect changes to predetermined paths in Windows and Linux systems.
- Identify vulnerabilities such as where an application may have a cryptographic algorithm vulnerability and recommend if patches or workarounds are available.
- Help identify specific services, ports, systems, and users
- Built-in asset discovery provides a dynamically updated inventory of what systems are operational in your environment, and what software is running on each.
- Discover and monitor assets running on-premises and in cloud environments (including Azure, VMware, Hyper-V, AWS, GCP)
3. Protect stored cardholder data
3.6, 3.7
- Monitor for changes to Office 365 policies, including data loss prevention (DLP), information management, and more.
- File Integrity Monitoring can detect when SSH or similar cryptographic keys are modified.
- Unified log review and analysis, with triggered alarms for high-risk systems.
4. Encrypt transmission of cardholder data across open, public networks
4.1, 4.3
- Identify when network traffic goes to unauthorized networks.
- Identify systems using compromised or insecure protocols that may increase their risk of being attacked.
- Monitor for changes to Office 365 policies, including Information Management and more.
5. Protect all systems against malware and regularly update antivirus software or programs
5.1, 5.2, 5.3, 5.4
- Identify systems susceptible to known vulnerabilities, or that may not have antivirus installed and/or operational.
- Identify for indicators of malware-based compromise, and orchestrate manual and automated actions to isolate infected systems and block malicious domains.
- Monitor and store events from antivirus solutions that could indicate a compromise, or attempt to disable antivirus software.
- Monitor for changes to Office 365 policies, including Information Management and more.
6. Develop and maintain secure systems and applications
6.1, 6.2
- Identify systems susceptible to known vulnerabilities, with systems ranked as 'high,' 'medium,' and 'low' risk vulnerabilities.
- Identify patches or workarounds available to vulnerable systems.
7. Restrict access to cardholder data by business need to know
7.1, 7.3
- Identify attempts to access systems using privileged accounts.
- Identify escalation of privilege attempts.
- Monitor for changes to Office 365 policies, including Information Management and more.
8. Identify and authenticate access to system components
8.1, 8.2, 8.5
- Aggregate logs and events from systems, applications, and devices from across your on-premises and cloud environments.
- Identify attempts to use retired or default user credentials.
- Monitor and alarm on Group Policy errors.
9. Restrict physical access to cardholder data
N/A
- Not applicable.
10. Track and monitor all access to network resources and cardholder data
10.1, 10.2, 10.3, 10.4, 10.5, 10.6, 10.7, 10.8
- Aggregate, analyze, and archive logs and events from systems, applications, and devices from across your on-premises and cloud environments.
- Identify logon success and failures.
- Identify privilege escalation attempts.
- Identify where systems are out of sync with the current time and/or Domain Controller, or for non-typical traffic on port 123.
- Identify unauthorized attempts to access or modify key logs.
- Identify where security tools, such as antivirus and firewalls, have been disabled or have failed to start.
- Captures all user account creation and modification activities.
11. Regularly test security systems and processes
11.1, 11.2, 11.4, 11.5, 11.6
- Assess systems for vulnerabilities, and where found rank them as 'high', 'medium,' and 'low' risk.
- Monitor access to and attempt to modify system and application binaries, configuration files, and log files.
- Monitor user and administrator activities in cloud environments such as Azure and AWS, and within cloud applications such as Office 365.
- Apply labels to alarms.
- Generate incident tickets within popular solutions like ServiceNow, directly from within the USM Anywhere console.
12. Maintain a policy that addresses information security for all personnel
12.1, 12.5, 12.8
- Monitor for changes to Office 365 policies, including Data Leakage Protection (DLP), information management, and more.
- Monitor all administrative activities through popular authentication and authorization solutions like Azure Active Directory.
- Monitor network traffic for violations of policy, such as communications that cross your cardholder data environment perimeters.