Executive summary
Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
AT&T Alien Labs® Open Threat Exchange® (OTX) recently created a pulse for a new threat entitled the RIG Exploit Kit which had been observed distributing ransomware to victim companies across a variety of industry verticals. This exploit was discovered by BroadAnalysis who outlined the exploit’s intricacies in a whitepaper that was released December 2, 2019. BroadAnalysis provided a step-by-step explanation of this exploit’s lifecycle, including all indicators of compromise (IOCs). Using the pulses created in OTX and threat intelligence from Alien Labs, AT&T’s Security Operations Center (SOC) was able to identify the initial behaviors of this threat and work in concert with the customer’s staff to mitigate the ongoing activity.
Investigation
Initial alarm review
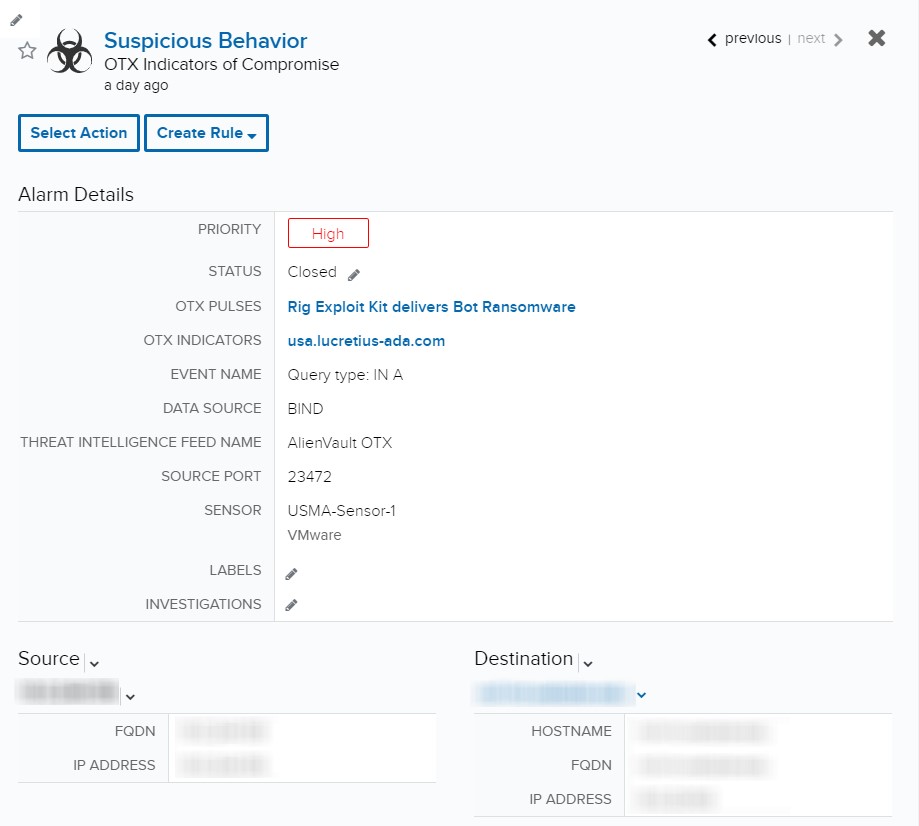
Indicators of Compromise (IOCs)
The initial alarm surfaced as the result of a Domain Name System (DNS) request to the OTX IOC usa.lucretius-ada[.]com, an IOC associated with the first stage of the cyber kill chain.
Upon further review, we realized this alarm triggered on the basis of a DNS request. After preliminary analysis, we determined the traffic did not directly correlate to an infection occurring on the endpoint, so we made the conscious decision to expand the Investigation.
Expanded investigation
Events search
Given the fact that we had a positive hit on the domain as an IOC, we then conducted a query for all events that matched this domain. Subsequently, we discovered twelve firewall events egressing to this domain from varying points of origin, other than the initial source found in the alarm. After aggregating the related events, we determined there were six unique sources that had established connections to this domain.
Reviewing these source devices, two appeared to be cell phones based on their hostnames, and the other devices appeared to be either user endpoints or possibly servers. These assets are not registered assets in USM Anywhere; thus, we were unable to derive additional information. Given the limited knowledge of the unregistered assets, at this point we had to rely on interfacing with the customer to verify if these devices were vulnerable and how best to plan our avenue for thwarting this threat.
Event deep dive
Now that we observed successful network traffic to the malicious domain, we turned back to the white paper from BroadAnalysis. The indicator we are matching is a specific URL on this domain. Reviewing the white paper, the indicator is:
- usa.lucretius-ada.com GET /zcvisitor/
We observed this URL in every firewall log from these six sources. At this time, we can confidently say that there are six devices who have successfully reached out to the malicious URL and that they are likely infected with this rig exploit.
Reviewing for additional indicators
After discovering these infected endpoints, we began building our notes for the Investigation. Simultaneously we reviewed the BroadAnalysis white paper to look for additional steps of the cyber kill chain being executed by these devices. Thankfully we were unable to discover any additional indicators and it appeared that we were still in the first stages of the exploit.
Response
Building the investigation
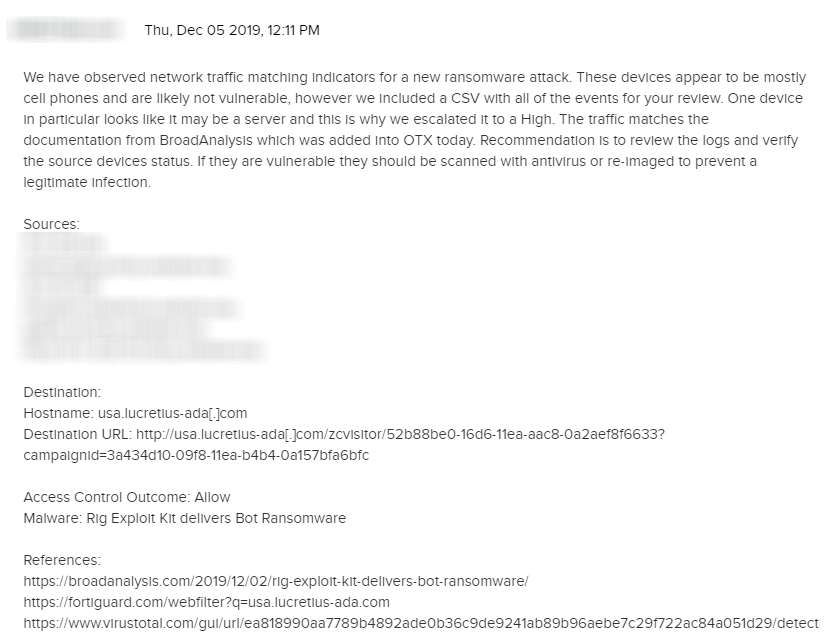
Given the urgency of the situation, we created a high severity Investigation for the customer. Utilizing the capabilities of USM Anywhere, we generated a CSV report with the full event activity we were able to observe so they could have visibility on the events and situation.
After attaching our report, we developed our notes to the customer with an analysis of what we observed, recommendations for what to do, and reference material for the indicators.
Customer interaction
Initial feedback from the customer was that they blocked the domain in their firewall to prevent future connection attempts. Additionally, they opened an internal support ticket to have the affected machines verified and re-imaged.
Limitations and Opportunities
Limitations
- During this Investigation we only had access to firewall and DNS logs. Due to this, we had limited forensic capabilities and relied heavily on the customer interaction for confirmation on what appeared to be malicious activity.
Opportunities
- Working with the customer to deploy additional AlienVault agents would allow us to gather more telemetry from the assets under investigation and more quickly triage the threat.