Executive summary
Multifactor authentication, or MFA, provides users with an added layer of security when logging into web applications. Surpassing its predecessor, two-factor authentication, in 2023, MFA is a standard option for another layer of security for online accounts. .
In May 2022, the Cybersecurity & Infrastructure Security Agency (CISA) published security advisory AA22-074A describing how default configurations within MFA applications are considered a vulnerability. The tactic was utilized by Russian state-sponsored cyber actors as early as May 2021 in a successful compromise of a US organization.
Based on this guidance from CISA, the AT&T Cybersecurity managed detection and response (MDR) security operations center (SOC) proactively scanned across our customer fleet and discovered a customer that was using the default configuration, which can be exploited. SOC analysts contacted the customer to inform them about the risk and provided recommendations on how to secure their network.
Investigation
Events search
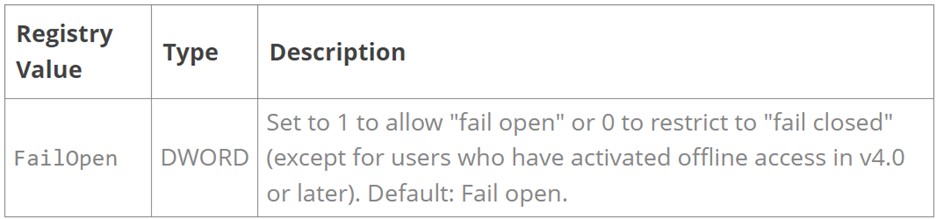
Analysts used the open-source tool, Elastic Stack, to search our customers for “FailOpen,”which is the default configuration within MFA applications that makes unauthorized access possible.

Event deep-dive
The search revealed a customer with their MFA application set to FAILOPEN = 1, which is the setting that allows for a malicious actor to bypass authentication when exploited. The “FailOpen” setting allows for an incorrect attempt at a connection, which would then permit unfettered access to an account with this setting on the customer network.
Reviewing for additional indicators
From there, SOC analysts pivoted to searching the customer environment for any information that would identify associated customer assets and accounts and that would indicate outwardly malicious activity. They discovered that the user responsible was listed as an administrator within the customer environment.
Response
Building the investigation
The analysts opened an investigation to address the misconfiguration in the MFA mobile application as well as to confirm whether or not the activity associated with the identified user was authorized. Included in the investigation was an explanation of the vulnerability as well as a summary of the involved user’s activity on the identified assets over the last 30 days.
Customer interaction
Analysts created a low-severity investigation, which in this case meant that they were not required to contact the customer. (Our MDR customers determine when and how the SOC communicates with them.)
However, to ensure that the issue was addressed in a timely manner, the analysts also notified the customer’s assigned threat hunter group, “The ForCE,” and the investigation was reviewed and addressed by the customer.
Ultimately, the investigation did not uncover any malicious events relating to the misconfiguration, but it illustrates how the AT&T MDR SOC is not only reactive but also works proactively to protect our customers.