Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers.
Executive summary
Our Managed Threat Detection and Response team responded to an Alarm indicating that suspicious reconnaissance activity was occurring internally from one of our customer's scanners. This activity was shortly followed by escalating activity involving brute force activity, remote code execution attempts, and exfiltration channel probing attempts all exploiting vulnerable DNS services on the domain controllers. The analyst was able to alert the customer to the activity before any successful exfiltration activity had taken place and the customer was able to confirm that it was a planned red team exercise.
Investigation
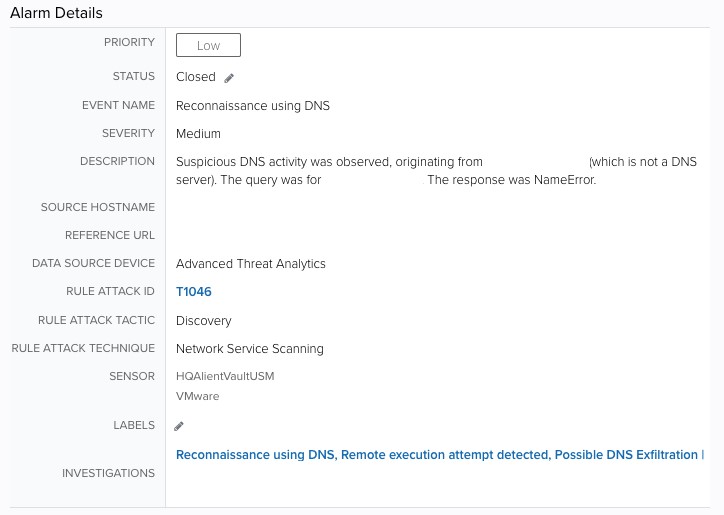
Initial alarm review
The initial alarm came from an Event in Microsoft® Advanced Threat Analytics that detected possible reconnaissance and discovery activity coming from an asset with a naming convention that indicated it was an enterprise scanner. Scanners frequently have external exposure, are typically easier to brute force against, and host multiple legitimate services like DNS, SMTP, SMB, that can be used to hide malicious activity.
Expanded investigation
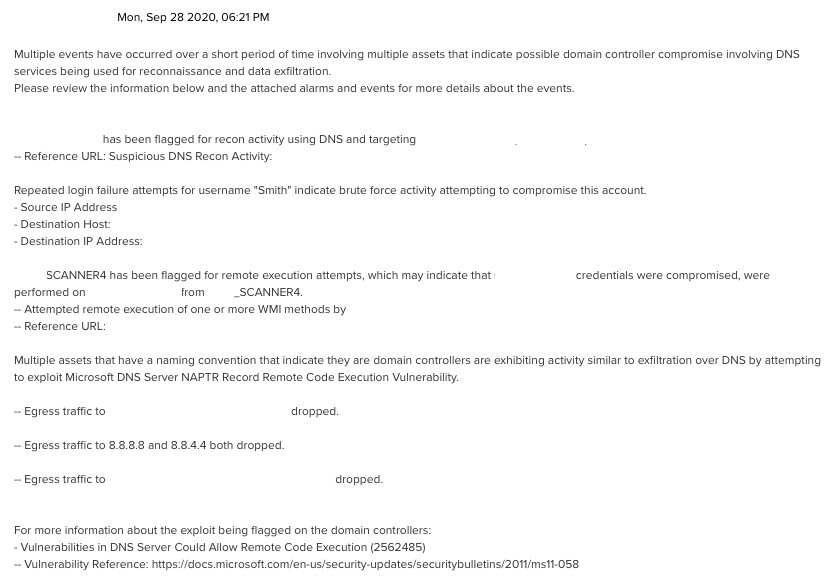
Soon after this, brute force activity and remote code execution attempts were reported involving Windows® Management Instrumentation (WMI) exploitation coming from a compromised service account that shared a naming convention with the scanner’s hostname, indicating the scanner and service account were compromised and now pivoting activity was occurring with the attacker attempting to gain further entry into the network.
These remote code execution (RCE) attempts were flagged with behavior associated with a DNS service vulnerability that had known patches available. Vulnerabilities in DNS Server Could Allow Remote Code Execution (2562485)
- Vulnerability Reference: https://docs.microsoft.com/en-us/security-updates/securitybulletins/2011/ms11-058
After the WMI RCE attempts were flagged, multiple assets with naming conventions that matched domain controllers generated alarms by attempting to contact well known external DNS servers. However this activity was also flagged as suspicious since these assets were not configured for DNS services or had previously been associated with DNS activity.
This, combined with the firewall events denying external traffic over port 53, indicated that these servers were not authorized to perform DNS services and that this activity was likely a probing attempt to find methods of exfiltration, such as DNS tunneling.
Response
The customer was alerted to the activity by the analyst and was able to confirm that it was part of a planned red team exercise. While this particular example was an internal effort, the customer commended our efforts at detecting the threat and responding quickly.