This blog was written by an independent guest blogger.
Network traffic analysis is the routine task of various job roles, such as network administrator, network defenders, incident responders and others. Wireshark plays a vital role during the traffic analysis; it comes pre-installed in many Linux OS’s, for instance, Kali. otherwise, it is available to download from the official website.
This article covers the traffic analysis of the most common network protocols, for example, ICMP, ARP, HTTPS, TCP, etc.
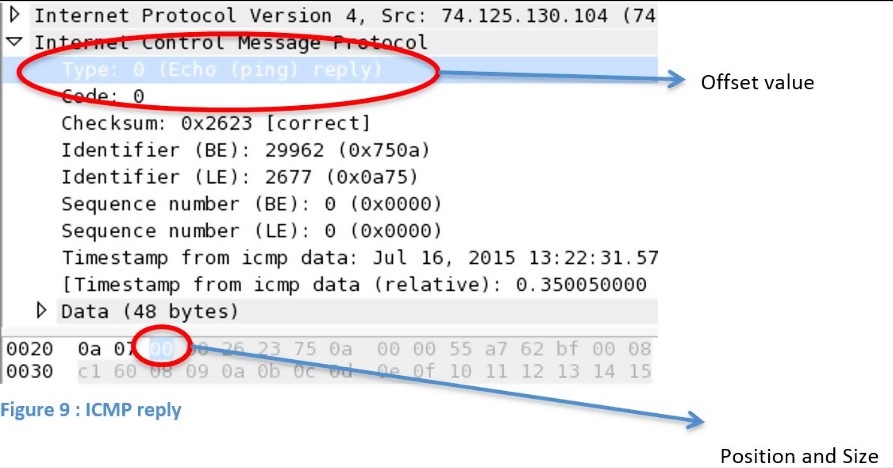
Capture filters with protocol header values
Wireshark comes with several capture and display filters. But a user can create display filters using protocol header values as well. Use this technique to analyze traffic efficiently.
proto[offset:size(optional)]=value
Following the above syntax, it is easy to create a dynamic capture filter, where:
- proto = desired protocol
- offset = header value
- size = data length
- value = data you want to find
Figure 1 Source: resources.infosecinstitute.com
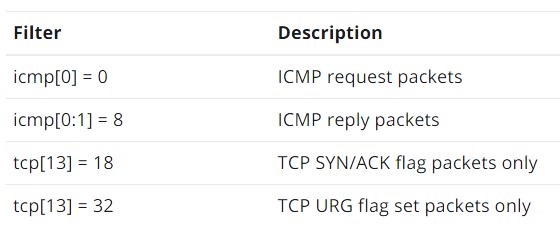
Some instances are in the following table:
Figure 2 Source: resources.infosecinstitute.com
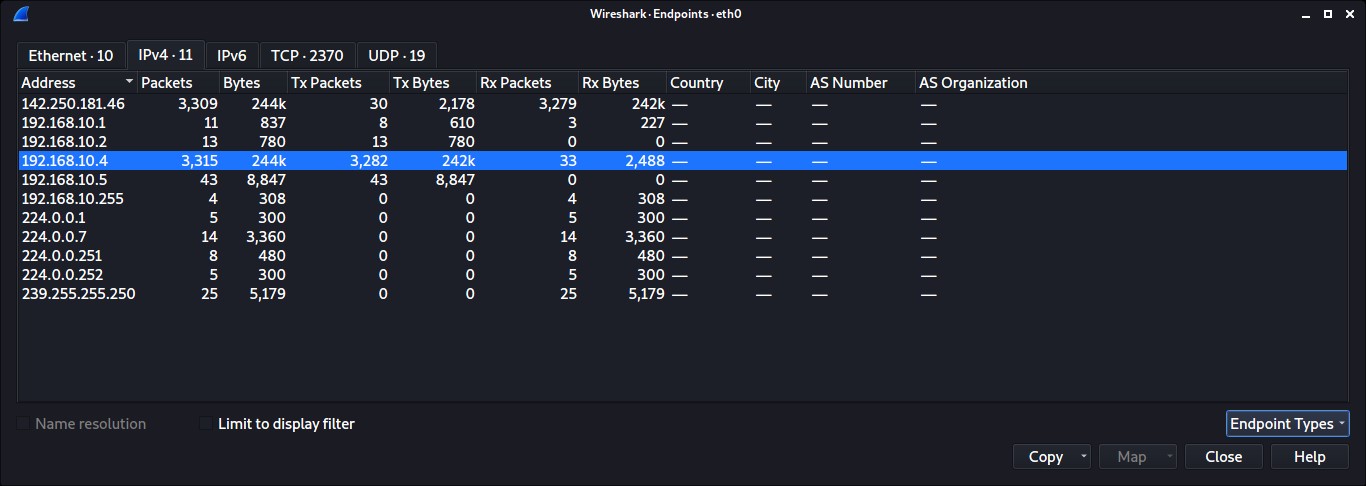
Analyzing endpoints
This feature comes in handy to determine the endpoint generating the highest volume or abnormal traffic in the network. To analyze the endpoints between two communication devices, do the following:
Capture traffic and select the packet whose endpoint you wish to check. -> Click Statistics menu -> Select Endpoints.
The most traffic-intensive endpoint, as seen in the picture below, is 192.168.10.4.
ARP traffic analysis
Address resolution protocol (ARP) generally uses to find the MAC address of the target machine. In this demo, let's try capturing and analyzing ARP traffic.
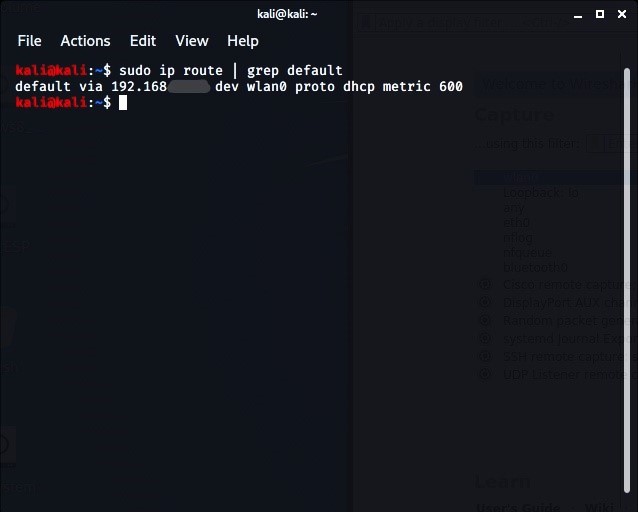
First things first, know the target machine IP. In our case, it's going to be the default gateway address.
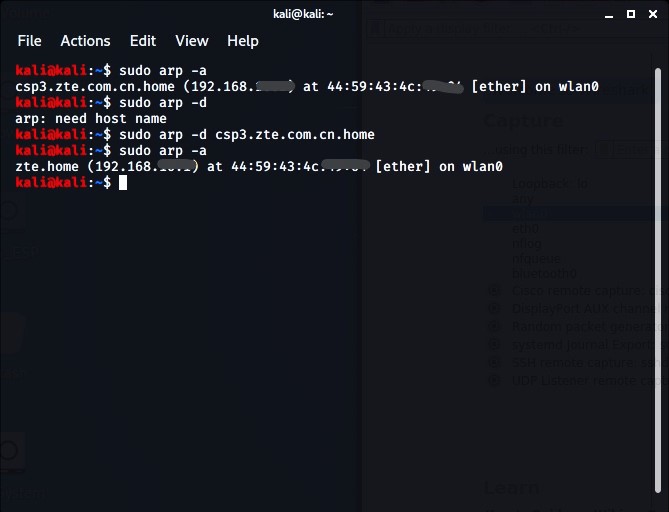
Find existing ARP cache -> Delete the existing one to understand the demo -> Check ARP cache for verification.
Start Wireshark data capturing, and ping the default gateway address -> Now, let's analyze what happens after removing the ARP entry and pinging a new IP address in the meantime.
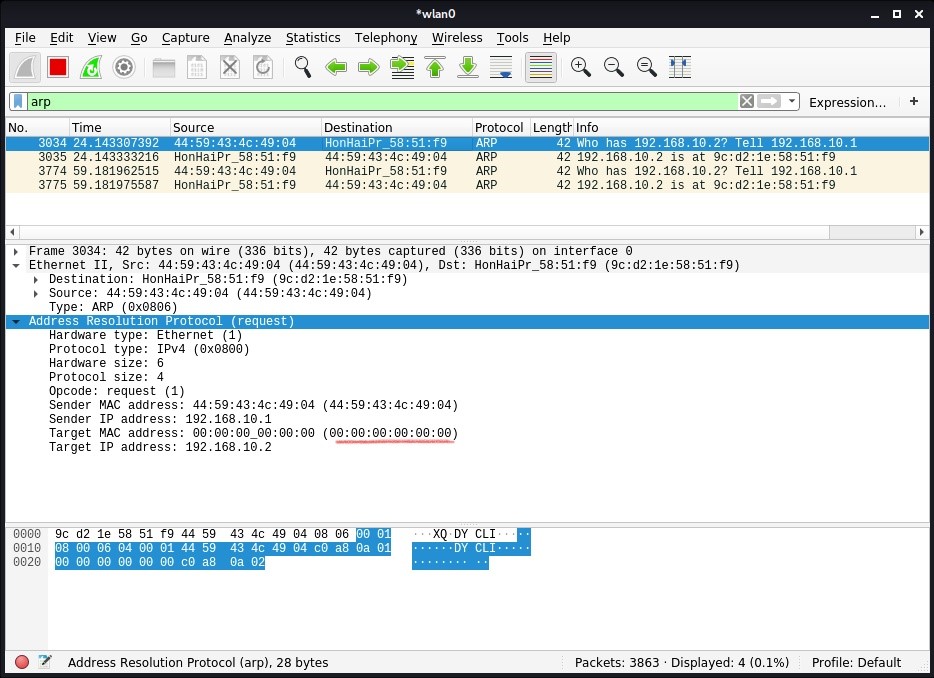
Analyze an ARP Request
Using the 'arp' filter, analyze the captured traffic in Wireshark.
Observe the packet request details from Ethernet and ARP; observe the source and destination IP and sender MAC and IP address.
Monitor the victim's MAC address. Since the destination MAC address is unavailable at the request packet stage, the victim's MAC address is zero, and the destination IP is the local system IP address.
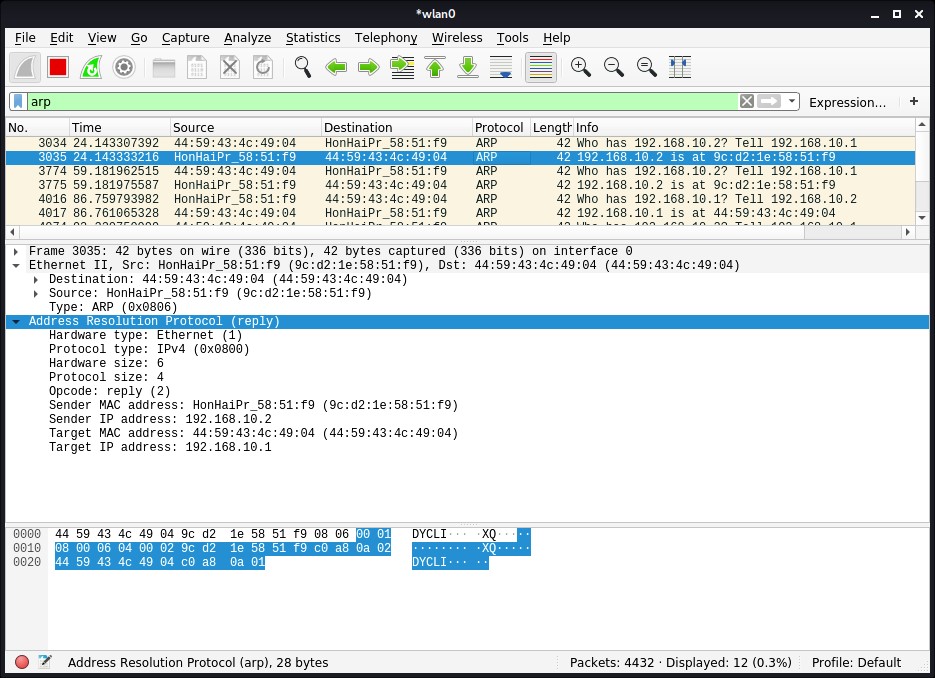
Analyze an ARP Response
Observe the packet replay details from Ethernet and ARP; observe the change in source and destination IP and MAC addresses.
The destination and source MAC address are switched in the response packet.
Everything is similar as before, except the target MAC address, which was all zeroes before. Now, that has turned into your MAC address.
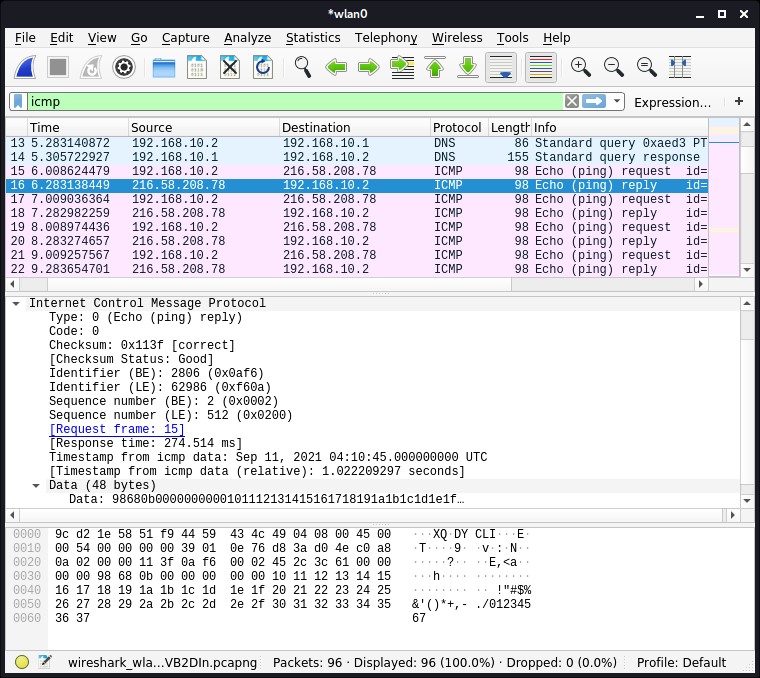
ICMP traffic analysis
ICMP is used for error alerting and monitoring to verify whether data arrives in a timely basis at its desired destination.
To capture ICMP traffic, ping Google.com. Use the ‘ICMP’ filter to see ICMP traffic. Click the ICMP echo-request packet from the Wireshark capture window and start observing the information.
In the request packet, the source IP is your (requestor) IP address. Whereas the destination IP is that of Google. You can also analyze the ICMP details like Checksum, Identifier Number, Sequence Number, etc.
In the response packet, observe the swapping of IPs between source and destination. You can also compare both request and response details, as they are similar.
HTTPS traffic analysis
The Hypertext Transfer Application Layer Protocol (HTTP) utilizes the internet to establish protocols whenever the HTTP client/server transmits/receives HTTP requests.
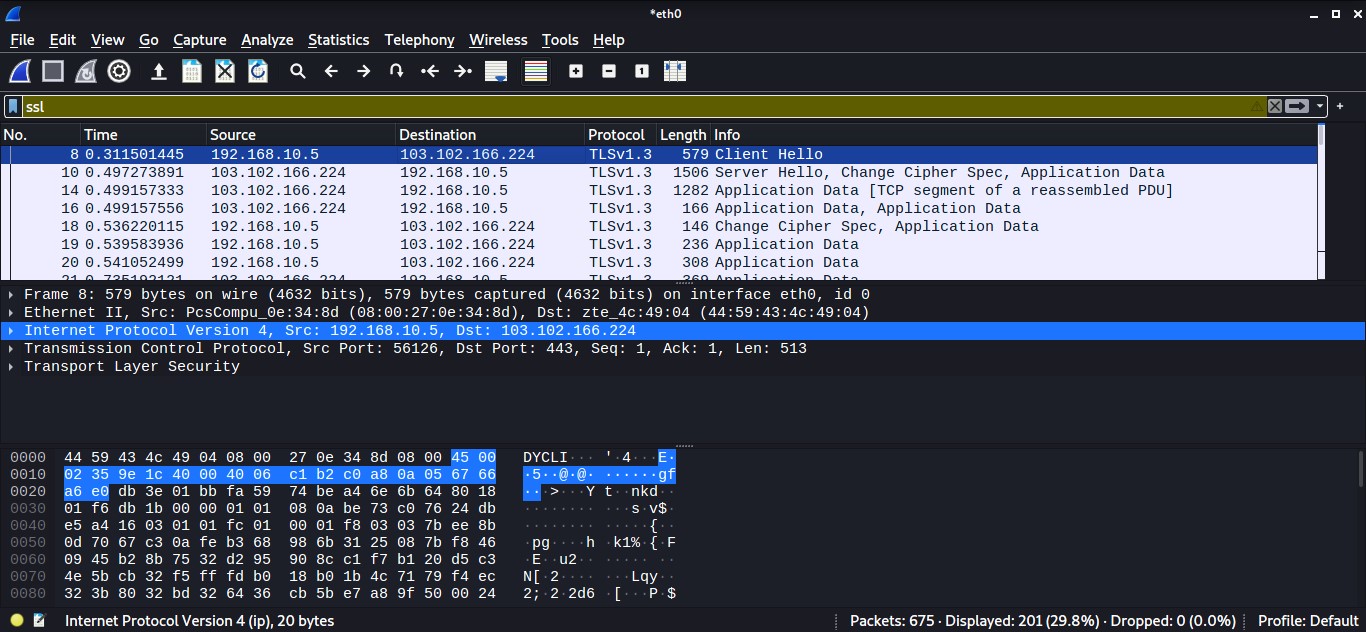
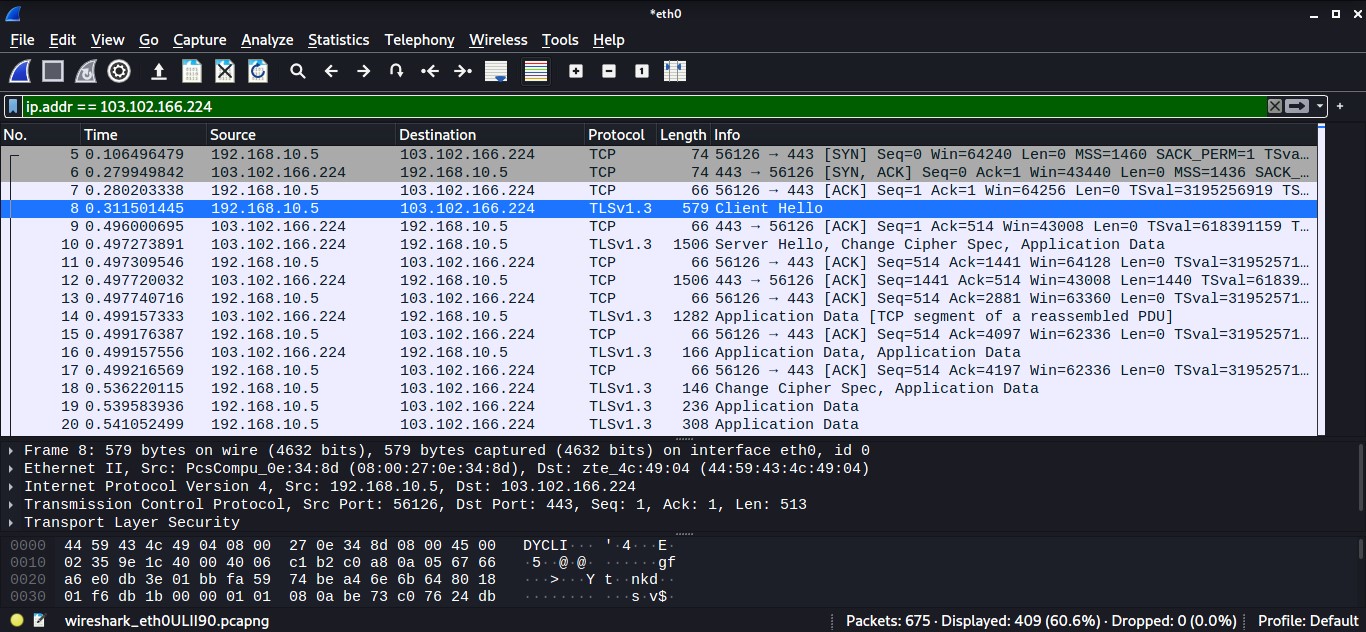
Start a Wireshark capture -> Open a web browser -> Navigate to any HTTPS-based website -> Stop the Wireshark capture.
Input ' ssl' in the filter box to monitor only HTTPS traffic -> Observe the first TLS packet -> The destination IP would be the target IP (server).
To see more traffic of the target IP (destination IP), input the following filter
ip.addr ==
TCP traffic analysis
A standard port scan takes advantage of the TCP three-way handshake. The attacker sends the SYN packet to the target port. The port is considered open when he gets SYN+ACK as a response, whereas the arrival of RST shows the port is closed. After receiving SYN+ACK, the hacker would send an ACK packet to establish a TCP connection.
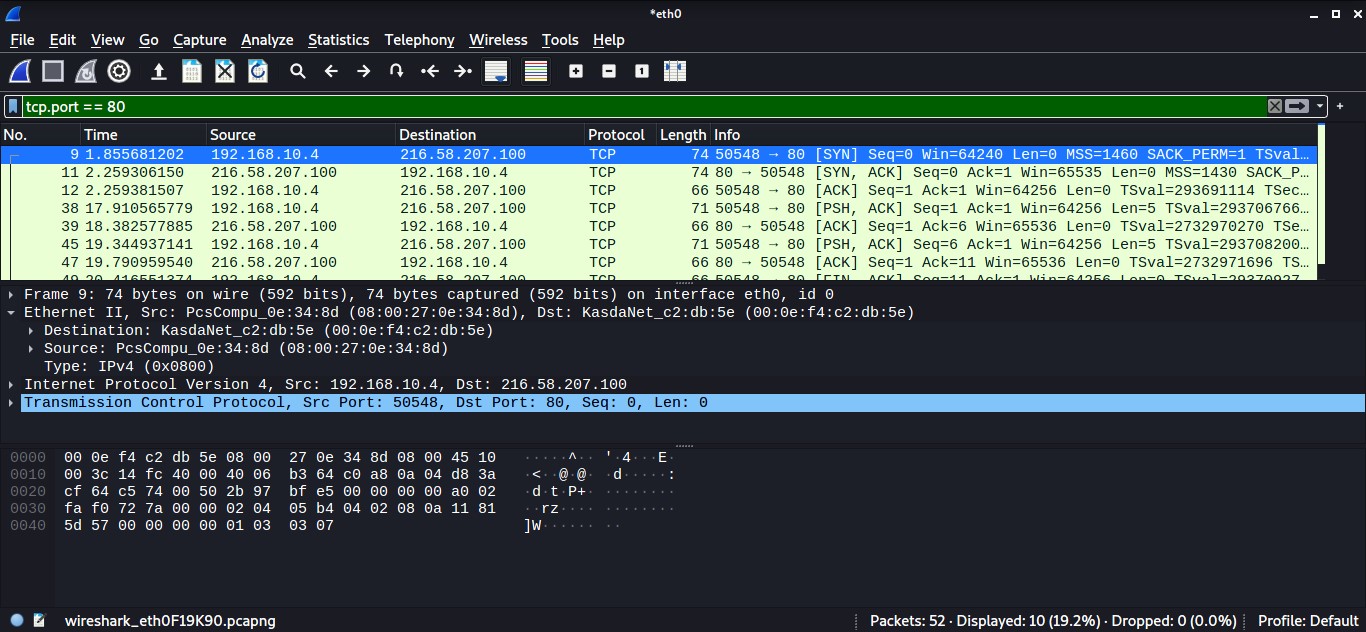
Let's analyze a TCP network traffic using telnet on Google port 80. Capture the Wireshark traffic while entering the telnet command.
Analyze TCP SYN traffic
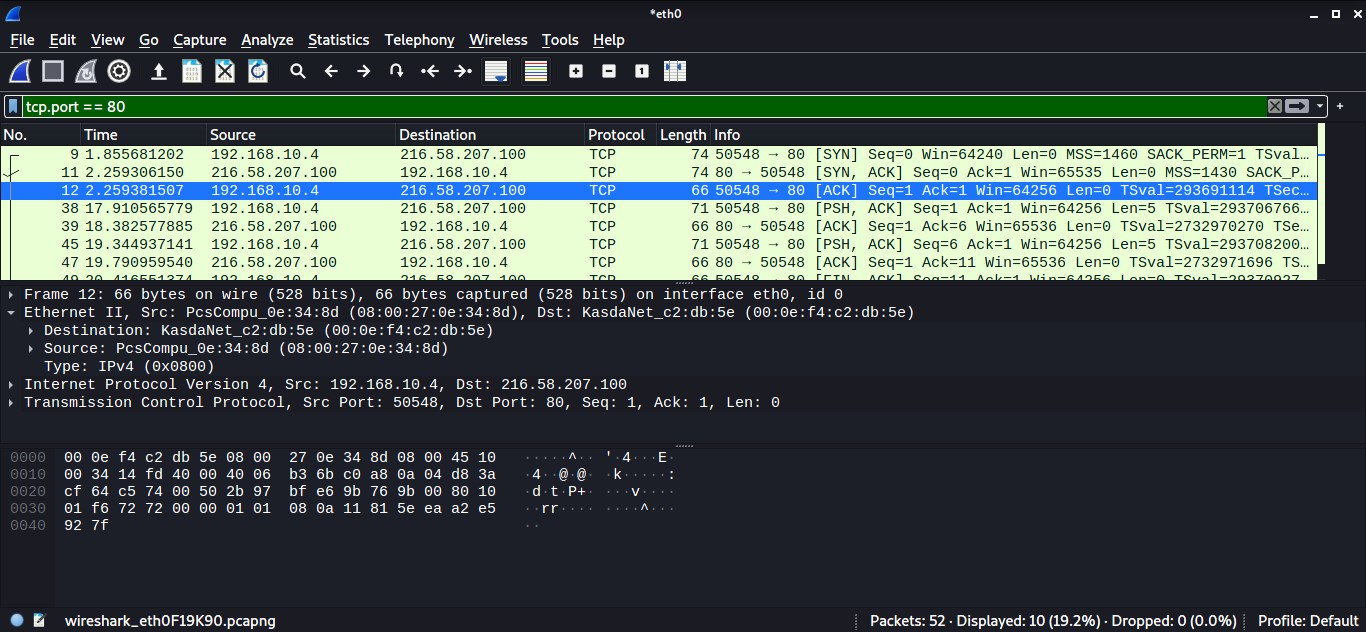
Input ‘tcp.port == 80’ to see only TCP traffic connected to the webserver connection.
Observe the TCP [SYN] packet. Expand Ethernet and observe the destination address that is the default gateway address; whereas, the source is your own MAC address.
To check the IP details, observe Internet Protocol Version 4; in our case, the destination IP is Googles' web server IP, and the source IP is the local IP address.
To view TCP details, observe Transmission Control Protocol, like port numbers. Monitor the flag values. SYN, which is enabled, shows the initial section of the TCP three-way handshake.
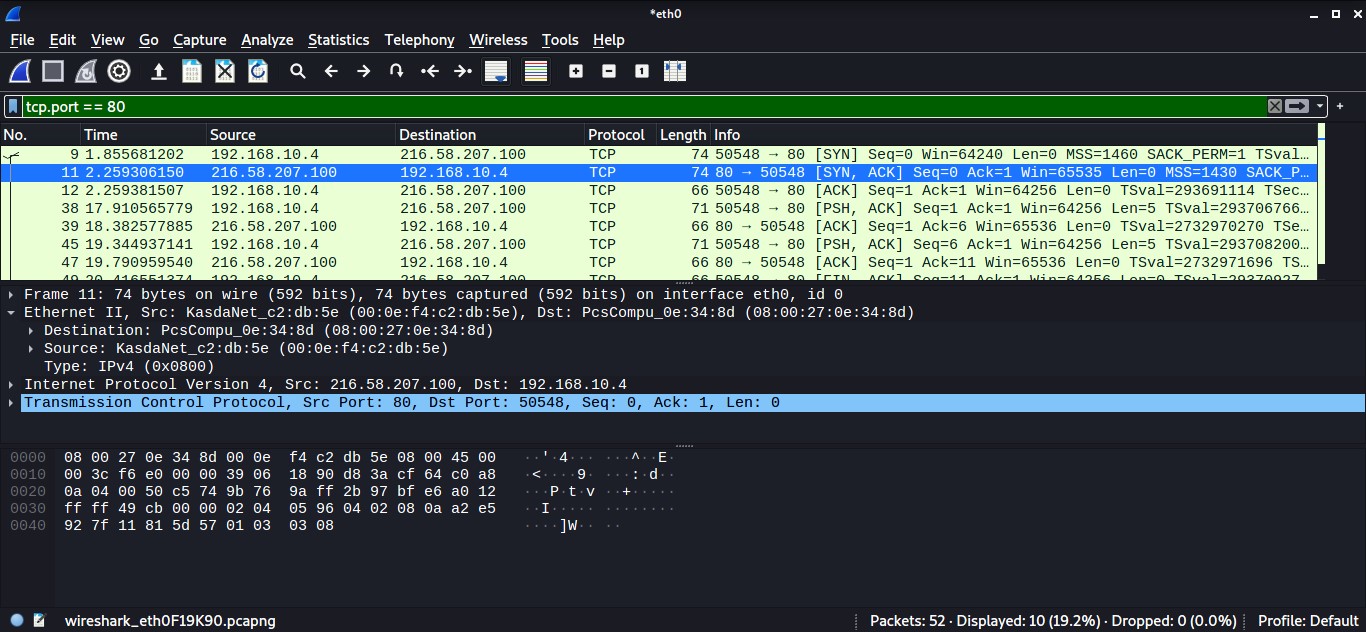
Analyze TCP SYN, ACK traffic
Take a look at the TCP [SYN, ACK] packet. Expand Ethernet and observe the destination address now would be your own MAC address; whereas the source is the default gateway address.
Monitor the acknowledgement code. It's worth noting that the number is one relative ACK number. The real acknowledgement value is one higher than the previous segment's identifier.
Monitor the flag values. [SYN, ACK], which is enabled, shows the second section of the TCP three-way handshake.
Analyze TCP ACK traffic
Now consider the TCP [ACK] packet. Expand Ethernet and observe the destination address that is the default gateway address; whereas the source is your own MAC address. To view TCP details like port numbers, expand Transmission Control Protocol.
The enable ACK flag signals that the TCP three-way handshake has reached the last phase. The client and server have started a TCP session.
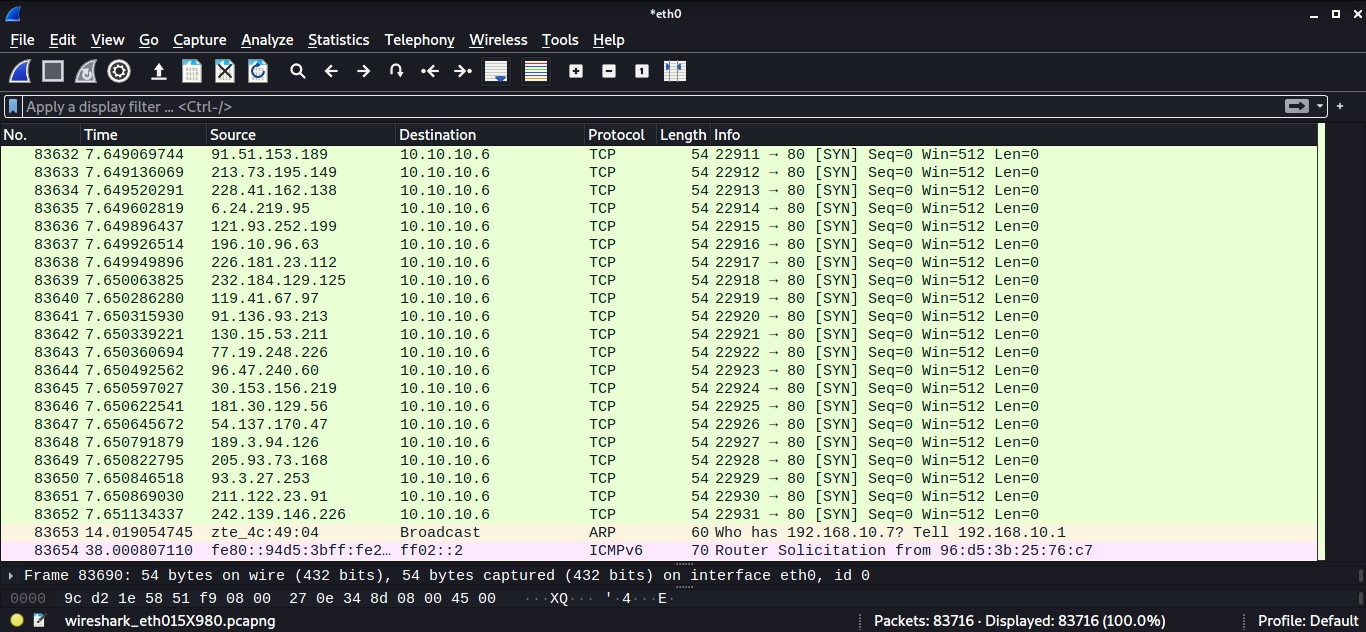
Analyze SYN flood attack
SYN flood occurs when an attacker delivers a substantial amount of SYN packets to a server using fake IPs, causing the server to respond with an SYN+ACK and keep its ports partially open, expecting a response from an invisible client.
By overwhelming a victim with SYN packets, an attacker can effectively overrun the victim's resources. In this state, the victim fights with traffic, which causes processor and memory usage to rise, eventually exhausting the victim's resources.
Use the hping3 tool to flood the victim IP. Simultaneously, start capturing the traffic on Wireshark. Input 'tcp.flags.syn == 1' in the filter box to view SYN packets flood.
Notice a lot of SYN packets with no lag time.
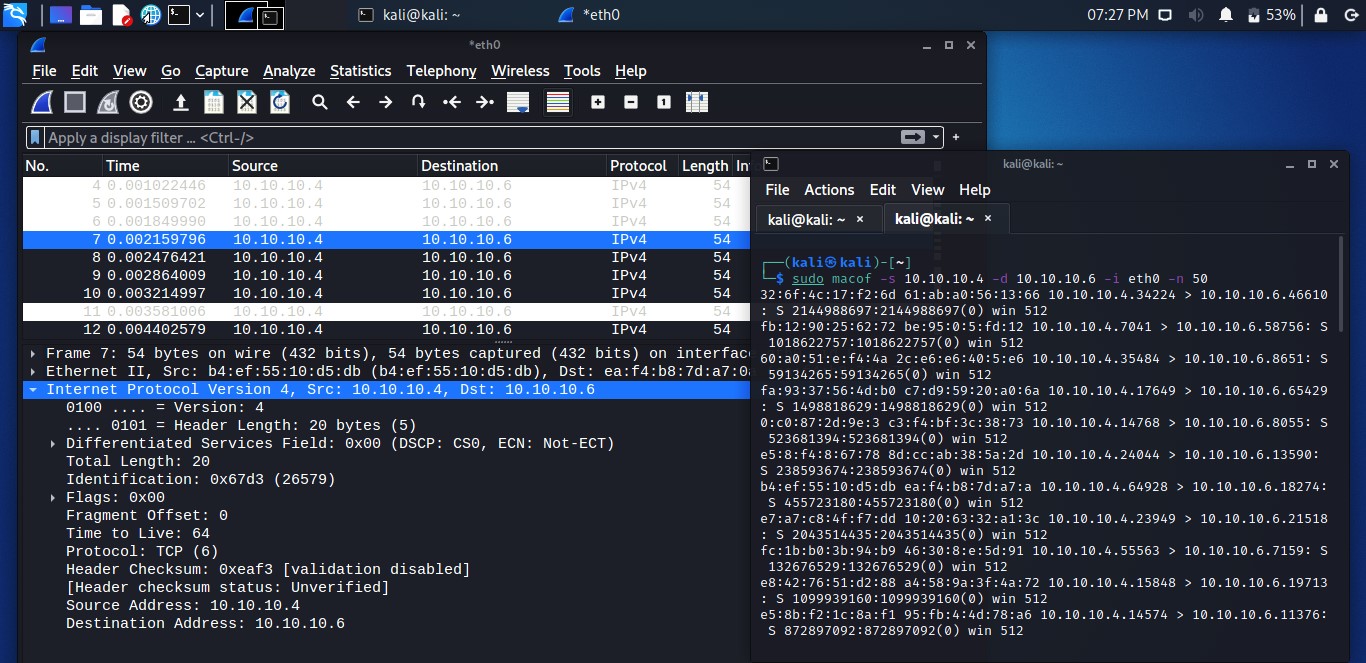
Analyze DoS attacks
Let’s simulate a Denial of Service (DoS) attack to analyze it via Wireshark. For the demo, I am using the macof tool, the component of the Dsniff suit toolkit, and flooding a surrounding device's switch with MAC addresses.
The image below shows IP address is generating requests to another device with the same data size repeatedly. This sort of traffic shows a standard network DoS attack.
For a DDoS attack, use the macof tool again to generate traffic. Observe the fake source and destination IP addresses are sending many packets with similar data sizes.
Conclusion
Wireshark is an essential tool that many blue team and network administrators use daily. The objective might differ, but they analyze network traffic using it. In this article, we have explored several network traffic types like HTTPS, TCP, etc. In addition, we have seen few attacks using Wireshark, like the DoS attack.