Multiple reports in the media, including in Bloomberg US Edition, allege that Russian-associated cybercrime group Killnet is responsible for a series of distributed-denial-of-service (DDoS) attacks during the week of October 6 that took several state government and other websites offline. While most of the websites were restored within 48 hours, these volumetric attacks can leave even the most secure sites paralyzed and susceptible to further damage.
AT&T Alien Labs, the threat intelligence arm of AT&T Cybersecurity, suggests politically motivated cyber strikes such as the ones that hit web sites in October are nothing new. Killnet has a long history of successfully attacking both public and private organizations and businesses.
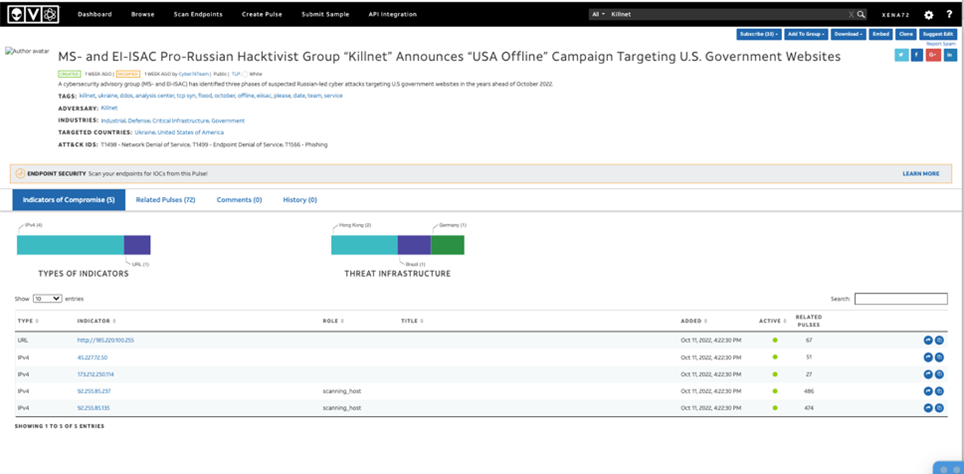
Research Killnet on the Alien Labs Open Threat Exchange (OTX),
among the largest open threat intelligence sharing communities in the world.
Figure 1: OTX pulse on Killnet.
“We have been following Killnet for years and have seen a marked increased activity in the last few weeks. Their attacks, however, appear to be opportunistic DDoS campaigns aimed at attracting media coverage,” says Research Director Santiago Cortes Diaz. “Their efforts seem to be coordinated with the Russian government as part of their FUD (fear, uncertainty and doubt) campaign around the geopolitical conflict.”
Aside from a temporary takedown that can disrupt operations, there is also a reputational cost to DDoS attacks. Moves against government websites potentially aim to destroy faith among voters that U.S. elections are a secure and insulated process. And, though the election process is mostly separated from the Internet, consecutive attacks of this nature could also negatively impact confidence in the United States’ digital defenses.
DDoS attacks, though typically short-lived, succeed in getting the public’s attention by causing a digital flood of information on websites with an otherwise regular flow of traffic. A botnet, a group of machines infected with malware and controlled as a malicious group, generates bogus requests and junk directed at the target while hiding within a site’s usual traffic patterns. DDoS attacks are not to be underestimated. They will likely continue to proliferate as hackers acquire access to more botnets and resources allowing them to commit larger attacks — and the resources will come with the next era of computing.
As organizations continue to deploy edge applications and take advantage of 5G, the threat of DDoS attacks is potentially compounded. To this point, in a survey of 1,500 global respondents for the AT&T Cybersecurity Insights Report: 5G and the Journey to the Edge, 83% believe attacks on web-based applications will present a big security challenge.
Why? Because along with the improvements in speed, capacity, and latency of 5G and edge computing, there is also going to be an explosion in connected devices. For example, in the same Insights Report, the top three use cases expected to be in production within three years for edge computing include: industrial IoT or OT, enterprise IoT, and industry-oriented consumer IoT functions — all of which are driven by applications that can be connected to the internet. This increase in devices and network quality as well as explosion in applications serve as fertile ground for targeted attacks from bad actors.
Though these recent attacks appear to have political motivation, businesses should be considering pro-active DDoS protection if they do not already have it in place. The relatively cheap and frequent nature of DDoS attacks are what make them very dangerous and costly to business continuity.
To learn more about AT&T’s DDoS service solutions, click here.