No business will argue against an enterprise-level security solution. With threats coming from every direction, a centralized security platform gives administrators the fighting chance they deserve to stave off malicious attacks.
Security information and event management or SIEM systems are considered to be the industry gold standard. While effective, knowing how to use SIEM solutions to reveal valuable insight can be tricky. Little surprise, then, that many are left frustrated or disappointed with SIEM use.
For the resource-strapped IT teams out there, we’ve compiled four SIEM use cases to make your business safer in less than an hour post installation. Read all about it below.
SIEM Use Case Example #1: Nagging SQL Injection Attacks
SQL injection attacks have been around forever. Reported first 10 years ago, these attacks still pose a threat to websites and databases. All it takes is a few malicious commands to make their way onto your SQL server, and it can be tricked into revealing sensitive information.
To prevent this, SIEMs give you several options. The first is the intrusion detection system (IDS), which scans for malicious content on your network targeting SQL deployments.
Here’s a sample report that shows this in action.
If your system has been compromised, IDS will alert you immediately. This lets you swoop in and take retaliatory action before data is siphoned off. Even if there’s no immediate danger, make it a habit to check up on systems running SQL to spot abnormalities.
Most SIEMs let you group your systems running SQL making this a breeze.
SIEM Use Case Example #2: Watering Hole Attacks
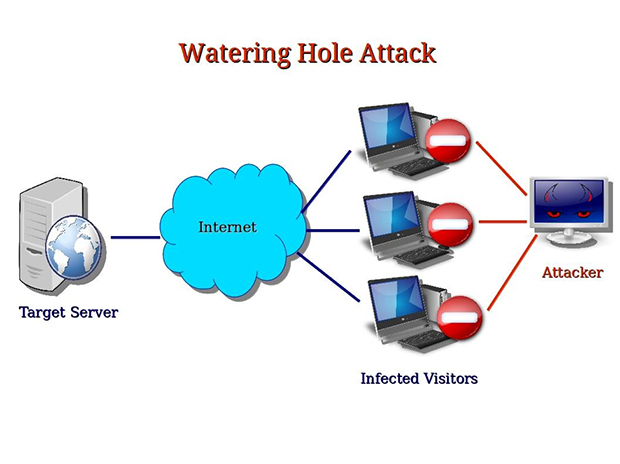
Hard to pull off but incredibly effective, watering hole attacks are difficult to detect. They use the same predatory trick seen in nature where an animal lurks around a watering hole waiting for a victim with its guard down to appear.
In the online space, this means one compromised site infects another. The attack begins when a target website is selected for infection. Common victims include government agencies and large enterprises. A profile of visitors that frequent this website is then built. The visitors in the profile are followed around the web as they visit other websites. When they land on a website with vulnerabilities, attackers inject it with malicious code. On repeat visits, the code redirects visitors to a third-party website where they are infected with malware.
When these visitors now revisit the target site, the malware will infect it.
SIEM Use Case #3: Malware Infections
Malware attacks remain popular as ever. Even the average computer user is aware of viruses, worms, spyware, Trojan horses, and ransomware attacks. Attackers rely on malware when trying to establish an initial foothold. Malware is preferred in these cases because of the ease at which it can be installed on a system.
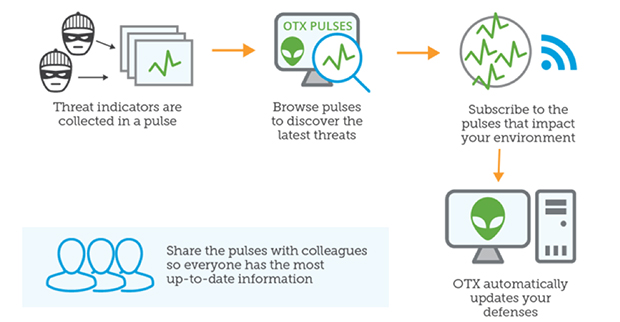
Traditional security technologies can’t keep pace with malware attacks. New malware is developed almost every day leaving most systems ill-equipped to effectively scan for potential threats. AT&T Cybersecurity's award winning SIEM lets you tap into around-the-clock community-driven data from the Open Threat Exchange to stay on top.
SIEM Use Case #4: Compliance
Meeting compliance and regulatory standards is critical. Any slip-up in meeting standards, like HIPAA or GPG13, can cost your business millions of dollars or even get it shut down. With competing priorities, limited budgets, and teams with varying expertise, it’s natural to let compliance-related tasks pile up. There’s a pressing need to find ways to better handle this process.
Enter SIEMs. Using SIEM, you can check on the compliance status of security processes across your system in one go instead of having to manually jump around each system. A centralized reporting dashboard gives you a bird’s-eye view of the location and compliance status of critical assets. Think of it as your one-stop shop for compliance maintenance.
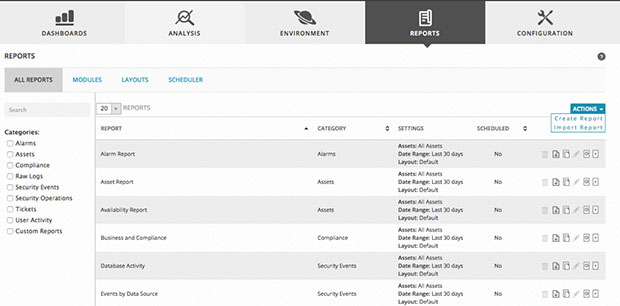
The compliance console pulls data from the following sources.
- Asset discovery
- Vulnerability assessment
- Host and network intrusion detection
- File integrity monitoring
The dashboard has hundreds of built-in reports, which means you can start right away. There are reports help you meet almost every compliant standard. A few examples include PCI-DSS, ISO 27002, HIPAA, and GPG13. If have unique reporting requirements, these reports can be easily customized to your needs.
Logs and Log Management
It must be mentioned that all of these use cases are made possible with correlated data from log files. This is another excellent topic for further learning. Learn about what kind of logs you need for a SIEM Implementation in this 3 part series of great, eductional blogs.
Conclusion
Companies both large and small must plan to protect their data. Failing to do so puts you at risk for financial trouble, legal liability, and loss of goodwill.
Make sure to deploy SIEMs to prevent such misfortunes befalling your business. If you know how to put them to use, SIEMs provide value out of the box. Here’s a quick recap on how SIEMs can benefit you with a few clicks.
- Prevent SQL injection attacks by keeping an eye on the health of your systems. This will keep you ready if and when attacks do happen.
- For handling watering hole intruders, SIEMs make it easy to monitor suspicious communication hinting at an attack in progress.
- If you’re worried about malware infection, community-powered data makes it likely that even new malware won’t be able to infiltrate your system.
- Ensure auditors and regulators don’t have a reason to turn off your lights with easy, one-step compliance status monitoring.
These use cases highlight just a few examples of what’s possible with SIEMs. You don’t need to spend days digging or hire experts to find valuable insight. Of course, if you take time to explore, the potential of SIEMs is really only limited by your imagination.


