Executive Summary
Cyber attackers are constantly innovating new ways to compromise users and steal credentials. Among these techniques, credential harvesting through phishing attempts is one of the most prevalent methods. This deceptive strategy often involves attackers creating a fake site that mirrors a legitimate login page. They distribute links to this phony site through sophisticated phishing emails, embedding redirect links that appear trustworthy through open-source intelligence (OSINT) but direct unsuspecting users to their trap.
Recently, the LevelBlue managed detection and response (MDR) security operations center (SOC) team responded to an alarm regarding a user clicking on a malicious link in a phishing email. The analyst recognized the threat as credential harvesting and quickly provided the customer with mitigation steps, helping to prevent further damage to the user and the organization.
Investigation
Initial Alarm Review
Indicators of Compromise (IOC)
To effectively respond to and investigate credential harvesting threats, it is crucial to recognize their signs:
- Mismatched URL: The displayed URL in the email or browser might not match the URL of the legitimate site it purports to be.
- Unusual page elements: Differences in formatting, language, or user interface compared to the genuine login page
- Suspicious redirects: The path taken by a link through multiple websites or unusually long URLs
- CAPTCHA tests: Often used on fake pages to make them appear more legitimate

Figure 1: Initial alarm with username and URL visited
In this case, the alarm shows that an email was sent with the subject line “[External] Document ready, Review and Sign Today Thursday-March-2024 19:20 PM.” This is a common format attackers use in phishing emails use to trick users into thinking there is a legitimate document that needs to be signed.
The screenshot shows the full URL contained in the email. When the analyst submitted the first domain in the URL ('www.samsonstonesc[.]com') through OSINT sites, it returned a clean reputation, which would indicate that this is a verified website; however, deeper in this link is 'ahmetorak[.]com,' and when this domain was submitted to various OSINT sites, it returned a malicious reputation.
Expanded Investigation
Events Search
Once the URL was identified as suspicious, the analyst performed the following:
- Deep link analysis: They investigated where the link led to as well as the reputation of each redirect or proxy domain involved
- Sandbox analysis: They copied the URL into a secure, isolated environment so its behavior could be observed without risk.
- Verify page authenticity: They checked for discrepancies in the fake page’s content and reviewed SSL certificates, and domain registration details against the expected values.
The analyst observed that the URL was redirected to a CAPTCHA screen, which once completed directed the analyst to a website masquerading as a Microsoft login page being used for a credential harvester.
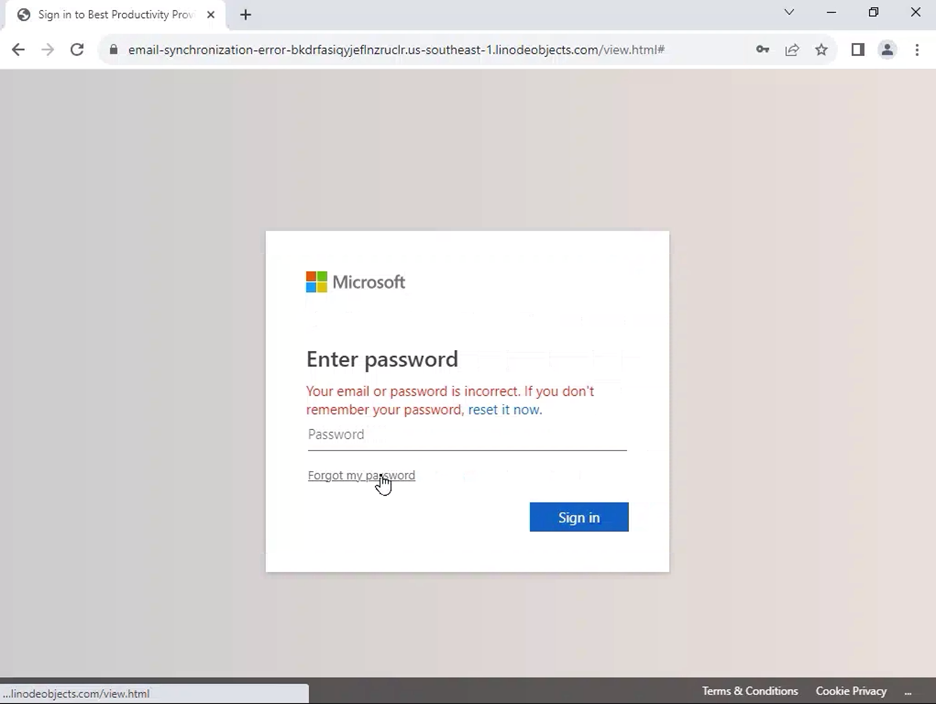
The below screenshot of this login page provides clear indicators that it is not a legitimate Microsoft login page and is in fact a credential harvester:
- The URL at the top of the page does not match that of an actual Microsoft page.
- Scrolling over “Forgot My Password” shows a link leading back to the fraudulent page.
Figure 2: Fake Microsoft login screen of the credential harvester
These websites are often hosted on an attacker’s server as a proxy. Once the user inputs their credentials, the attacker will receive this data and forward the user to a legitimate page. This makes it even more difficult for the user to understand that their credentials have just been stolen.
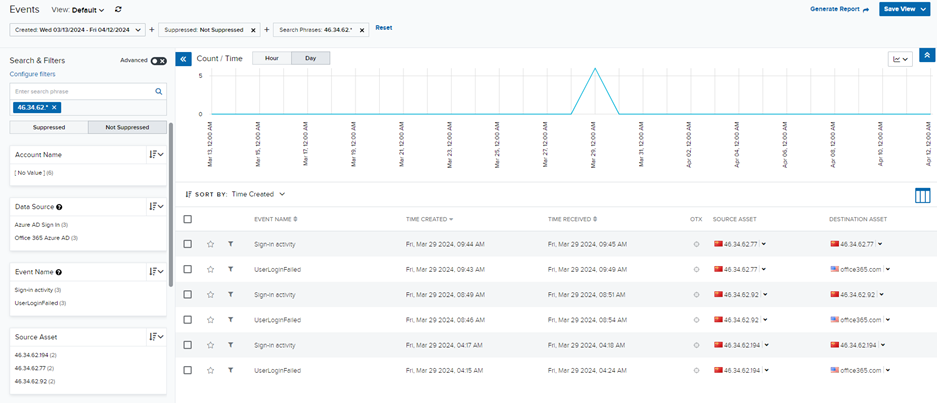
Figure 3: Login attempts for affected user from Chinese IP address
After the user clicked on this link, the LevelBlue MDR team began observing login attempts from a Chinese IP address.
While the team did not have direct evidence that the user input their credentials, they could infer it through these login attempts, and the events shown were added to the investigation. The threat actor likely received the user’s email and password from the credential harvester and attempted to log in from this Chinese IP address to perform additional malicious activity. If the login attempts had been successful, the attacker could have caused further damage to the user and organization using this compromised account.
Response
Building the Investigation
The MDR SOC team quickly alerted the customer to the threat by creating an investigation that detailed the malicious behaviors observed, provided evidence of traffic to this URL and the login attempts from the foreign IP address, and revealed the discovery of compromised credentials.
They also relayed the steps that should be taken to mitigate the threat, which included:
- Locking the affected user accounts
- Revoking any active sessions to prevent further unauthorized access
- Resetting credentials to eliminate access with stolen information
- Implementing multi-factor authentication (MFA) to enhance security measures and reduce the likelihood of future breaches
Conclusion
The analyst’s due diligence and rapid response allowed the customer to perform the recommended response actions before the attacker could succeed in gaining access. The incident highlights the importance of having robust detection in place so threats such as credential harvesting can be quickly identified. It also highlights the need for organizations to educate their users on the signs of phishing and credential harvesting and to enforce strong authentication measures such as MFA to protect against increasingly sophisticated cyber attackers.