Insiders, moles and compromises
According to a recent SANS survey on the security of the financial services sector, the number one threat companies are concerned about doesn’t relate to nation-states, organised criminal gangs or ‘APTs’. Rather the main worry revolves around insider threats – but what exactly is an insider threat and what can be done to detect and respond to these threats?
A new old problem
The discussion around insider threats has increased recently, in the financial sector and in other areas as well. Part of this may be attributed to the spotlight Edward Snowden shone on how much damage an employee can cause to an organisation - even one as secretive as the NSA.
But insider threats are nothing new. During the height of the cold war, many spies defected to opposing sides, taking with them national secrets and expertise right from under the noses of their spy bosses. As a result, many counter techniques were developed and deployed to keep an eye on insiders with valuable knowledge or skills to prevent would-be defectors to make an escape or pass over information.
What is an insider threat?
When it comes to trading state secrets, identifying an insider threat is relatively straightforward. But in today’s environments, the definitions start to blur somewhat.
We can define an insider as an individual with legitimate access within the corporate perimeter - be it physical or virtual. This would include permanent and temporary employees, 3rd party contractors as well as 3rd party support companies and outsourced service providers.
Typically, a threat is defined as something or someone exploiting a vulnerability in a target. In the case of insiders, this can be reframed as someone abusing their trust.
Therefore, we can summarise the insider threat as someone who misuses the legitimate access granted to them for the purposes of self-interest that could potentially harm the organisation.
A question of intent
Unfortunately, whenever humans are involved, no case is so straightforward, particularly where the malicious behaviour emanates from within the circle of trust. Differentiating malicious insider behaviour from user error, or even legitimate activity can be a challenge.
For example, a user is seen to download a number of files onto their personal device. It could be they are about to tender their resignation and want to take some information with them to their next job. Alternatively, it could be a hard-working and loyal employee wanting to catch up with some work over the weekend. Or worse still, it could be that the users account has been compromised and is being under the control of an attacker masquerading as an insider.
Types of insiders
With this in mind, we can break down insiders into three broad categories
- Non-malicious insider
- Malicious insider
- Compromised insider
Non-malicious insiders are those users that perform actions, which have no ill intent, but can nevertheless cause harm to an organisation. Such actions could include user error, such as running commands against a production environment believing it is development or losing a company laptop. It can also cover users which are trying to fulfil their job by using non-approved tools. Shadow IT users fall into this scope, where users will procure or use a cloud application such as a file-sharing app to increase productivity, but inadvertently expose the company.
Malicious users are aware of their actions and the negative implications on the organisation, yet still pursue that course of action. This grouping includes a broad set of users.
Users which are leaving the organisation may harvest information they believe would be of use to them in future jobs. Whilst they are often aware their actions are in violation of company policy, actions are often justified with a sense of entitlement.
It will also include users that are disgruntled for one reason or another and seek to vent by causing as much disruption or damage to company assets. Activists or employees who feel whistleblower processes are insufficient will also react in a similar manner.
At the highest level will be employees engaged in corporate espionage. Providing intellectual property or other sensitive information to competitors, criminal gangs or nation-state sponsored actors.
The final oft-overlooked category is that of compromised insiders. Typically this is where credentials have been guessed or captured as part of a targeted attack. Although the actor behind the account is not an employee - the use of legitimate credentials would show up as if it were an employee.
The insider risk matrix
These factors combined can be represented in the following matrix where intent is measured against harm.
For example, a company may deem that the risk of shadow IT, i.e. users procuring their own SaaS applications within which they could upload sensitive company data that could be accessed by non-authorised persons, or the SaaS provider could be breached.
In this case, the intent would be non-malicious in that the user was trying to perform their job, yet the consequences could be significant.
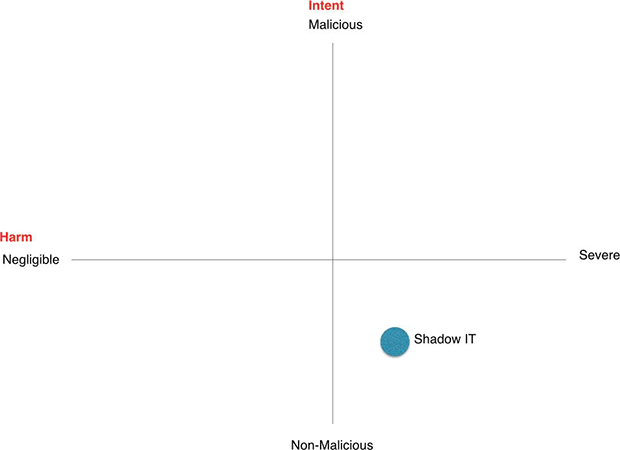
Other insider threat scenarios could be plotted in the same way to visualise which threats are more severe overall by how far they are positioned up and to the right.
From a risk perspective, this alone won’t tell the full story as we are still missing the likelihood. The likelihood can be represented by the size of the bubble on the chart as depicted below.
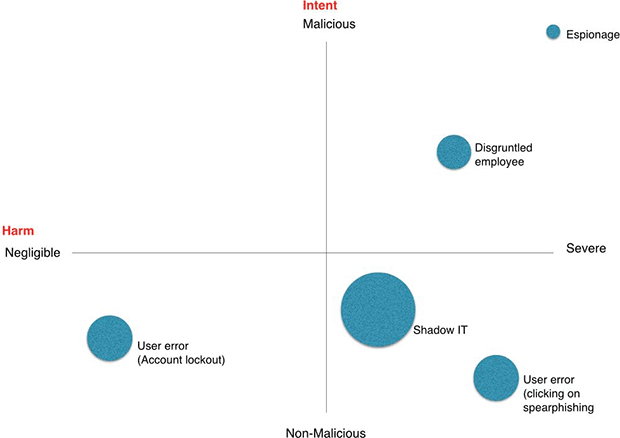
The size of the bubbles (likelihood) help visualise that whereas espionage can have the biggest impact and is undertaken with the most malicious intent, the likelihood of it occurring is potentially less than that of a disgruntled employee or even shadow IT proliferating within the enterprise.
User error encompasses many activities – all of which are non-malicious in nature, however the harm caused could range from negligible such as an account lockout through to severe by allowing an attacker a foothold inside the network by clicking on a phishing link.
Detecting insider threats
Perimeter and preventative controls are largely ineffective in detecting or responding to insider threats, as by their very nature these are threats from within.
As a result, different techniques should be deployed to address each type of specific threat based upon the manner in which it manifests. Like many security controls, the concept of defense in depth can be applied whereby a collection of procedural, user and technical controls can be applied to detect suspicious insider activity, as depicted in the controls pyramid below.
Procedural and user controls
Procedural and user controls are important to get management support and ensure policies implemented are acceptable from a legal as well as cultural perspective. Privacy is a discussion topic that comes up frequently and having transparency in how a company uses data it collects about its employees is required in retaining trust. It also provides a framework whereby aggrieved employees can escalate issues without the need to resorting to conducting harmful acts against the company.
Finally, it also raises awareness so that employees can potentially detect and alert suspicious activity.
Technical controls
The technical controls are an area which has seen a lot of development in recent years. This primarily focuses on analytical techniques to identify suspicious user activity. Primarily these will baseline user activity against its own past actions in addition to base lining against peer activity to identify outliers. The baselines can be set against logins (times / locations), file or system access, network traffic or even endpoint activity amongst others.
Threat intelligence can also be a valuable asset in understanding whether outbound traffic is communicating with known command and control or other suspicious transfers.
In addition to these techniques, traditional technologies can also be utilized to try and identify suspicious activity that may point towards a rogue insider. Endpoint or network DLP (data loss prevention) tools can monitor where excessive files are being exfiltrated out of the organisation. SIEM rules can also be tuned to alert on certain events that are indicative of malicious insider activity.
Emerging techniques
Alongside threat intelligence, a number of newer approaches are being developed which can directly or indirectly assist in finding insiders. Social media channels play an ever-increasing role in both legitimate and not so legitimate communications. Having the ability to monitor these channels, particularly where enhanced by specific threat intelligence greatly increases chances of isolating activity on these typically out-of-band channels.
Sentiment analysis is another tool in the arsenal that has is garnering more interest. It seeks to identify where an employee may be disgruntled or activist-tendencies which are contrary to the business values.
Response
One of the challenges with any form of detection technology is having adequate skills and resources to investigate and respond to alerts. For this reason, some technologies and businesses are moving to more of a reporting framework for insider threat detection as opposed to raising alerts.
With reports, a broader picture is painted around a user and their activity, thus allowing investigations to be conducted based on richer context versus merely a one-off alert. Such mechanisms could include a risk-score against each user based on a number of factors such as grade, access to information, length of service, recent appraisal and so on.
Whichever method is adopted, it will still require manual effort to investigate and validate any suspicions of wrongful behaviour.
Battle of attrition
Whilst many new techniques have been developed and are continually being developed to detect and respond to insider threats – dealing with humans, particularly trusted employees requires a different strategy and approach than dealing with malware.
Whereas any suspicious email or file can be relatively easily quarantined or blocked until proven otherwise – employees cannot be suspended or fired based on a couple of indicators or mere suspicion. Also, bear in mind that a large portion of suspicious activity can take place outside the realm of IT systems. This means that companies will need to work with HR and legal departments in advance to determine the best strategy to investigate suspicious activity and how to interact with suspected employees.
It becomes a matter of balancing risk – a company may be able to recover a lot easier from an ex-employee taking a copy of the customer database than from an unfair dismissal lawsuit. In the financial sector especially, the stakes are high all around.