Yesterday, many people received an e-mail from someone they knew and trusted asking them to open a "Google Doc.” The email looked, felt, and smelled like the real thing—an email that Google normally sends whenever a share request is made. However, the email contained a button that mimicked a link to open a document in Google Docs.
When users clicked on the button, they were prompted to give “Google Docs” permission to read / send email, manage their email, and access their contact lists.
In reality, this was a malicious application registered by the attackers. And, in fact, is one of the most well-crafted phishing attempts in the last year.
By clicking on the ALLOW button, users authorized the malicious application to perform actions on their behalf. The users’ browsers were redirected to one of the malicious servers set up by the attackers, for example:
https://googledocs[.]docscloud[.]win/g.php.
The AlienVault Labs Security Research Team detected the activity, and while the attack was still in progress, we created a Pulse in the Open Threat Exchange (OTX) with all the indicators of the infrastructure the attackers used (mainly the domains they used in redirection).
In addition, several OTX users jumped in and shared more malicious infrastructure in a matter of minutes!
This helped get the indicators out immediately to the 30,000+ people that follow the AlienVault OTX account. Kudos to the OTX members who jumped in and delivered this valuable information so quickly to the community!
Sign up to OTX to join the 53,000+ users who already benefit from this free service >
Going back to the attack–when the user was redirected to one of the servers after allowing the malicious application to perform those actions, it was served with the JavaScript code that contained the self-replication / worm functionality.
First, the malicious JavaScript would get access to the contact list (first 1000 entries):
The code parsed the names and email addresses of those contacts and then prioritize addresses from gmail.com, avoiding addresses containing the words “google”, “keeper” and “unty”.
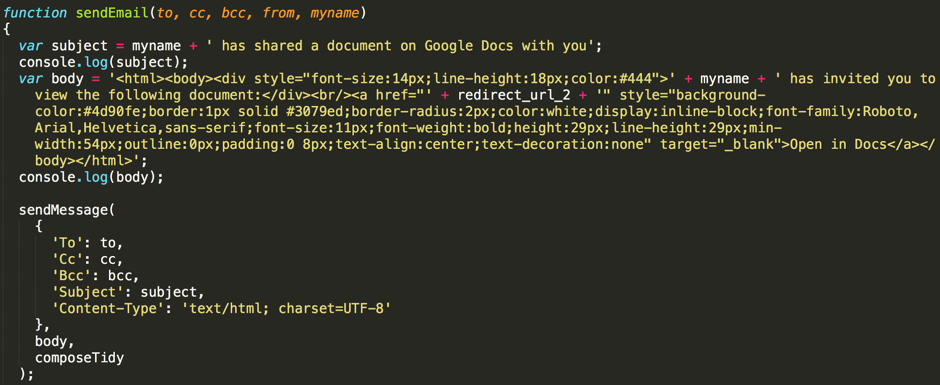
Once the list of potential victims was crafted, the code sent the same email to them as well, thus propagating the attack:
When sending the email, the attackers also decided to BCC the address hhhhhhhhhhhhhhhh[at]mailinator[.]com -, presumably to monitor progress or collect the list of victims.
Impact
Luckily, Google reacted to this quickly, and the malicious applications were shut down in about an hour after the start of the campaign. Cloudflare, which the attackers used in front of the malicious infrastructure, took down that part of the attack infrastructure quickly, too.
It is important to mention that the attackers didn’t exploit any vulnerabilities in Google services or OAuth. They simply leveraged a built-in capability that was designed to be used in this way to serve their nefarious intentions. The main problems from my point of view were:
- User Interface: This is not the first time that attackers used this trick, and it is probably going to get worse. Google and other providers could probably improve the UI to display more information about the application / author, alert the user of the dangers, and more. A similar issue was reported to Google in 2014
- Application review process: Google and other providers (Office 365, Yahoo, etc.) need to improve the review process for applications requesting access, especially those that look suspicious or ask for specific permissions. They could even start with reviewing applications that use suspicious names such as “Google Docs”.
Blame the bears
As I mentioned earlier, this is not the first time this technique was used. Multiple actors have been using it for years to circumvent two-factor authentication. One of the infamous groups using this technique went by APT28/Fancy Bear/Sofacy, or for those of you not familiar with the fancy names, the group behind the DNC hack. You can read more about that particular attack in a great report released by TrendMicro, which describes how the group used this technique to convince users to click on a malicious application with the name “Google Defender” (instead of Google Drive”).
As we have seen repeatedly, attackers learn from each other all the time and, unfortunately, we are going to see this technique adopted more and more by many different actors.
The importance of monitoring cloud applications
G Suite, like Microsoft Office 365, has become a widely-used cloud service by individuals and organizations worldwide for document sharing and email. However, the same services that make it possible for users to share documents and collaborate can also be used to compromise accounts as malicious actors search for new ways to phish information and compromise systems and data in the cloud.
As enterprises continue to adopt cloud services and applications, it is important to make sure that you have the right tools in place to deal with threats in those environments. Traditional security tools fall short, and most IT security teams don’t have the time, resources, or tools available to properly monitor cloud services like G Suite. Although Google, Microsoft, and other cloud service vendors invest a lot of time into ensuring the security of these cloud services, the weak link will always be the end user. As in the case of the threat described in this blog, users can easily be tricked by malicious actors into clicking on something that is malicious and harmful. Having visibility into that user activity and monitoring that activity to identify malicious or suspicious behavior is critical to maintaining a healthy security posture and protecting your infrastructure.
AlienVault USM Anywhere, a cloud-based solution for cloud and on-premises security monitoring, is designed to help you monitor all your business-critical infrastructure from a single console. With the ability to monitor user activities in cloud services such as G Suite, Office 365, AWS, and Azure, USM Anywhere provides a comprehensive, complete security monitoring in a single pane of glass.
USM Anywhere enables users to monitor their infrastructure to detect threats, respond to incidents, and meet their compliance goals. It includes the essential security capabilities, including asset discovery, vulnerability assessment, intrusion detection (for the cloud, network, and host), SIEM, and log management, as a unified solution to give you visibility into your infrastructure and quickly identify the threats that can lead to compromise.
How USM Anywhere Helps
As you know, threats change over time. Threat actors are constantly developing new techniques to trick users and compromise accounts. The traditional approach that most IT security teams take is to buy more solutions to solve the new problem of the day. This is, however, unsustainable and leads to tool proliferation. Organizations find themselves trapped in an endless “threat cycle.” Buy a tool to address a threat. The threat changes. The tool is no longer effective. Buy a new tool. The threat changes, and so forth and so on. It’s Groundhog’s Day in real life, but without the joy of Bill Murray.
AlienVault solves the problem of the threat cycle with the USM Anywhere platform and its AlienApps™ architecture. Building on the Unified Security Management™ (USM™) approach pioneered by AlienVault, the USM Anywhere platform takes the unified approach beyond the five security essentials. The highly extensible USM Anywhere architecture allows AlienVault to seamlessly add new security technologies into the platform as they become available, allowing you to keep pace with the ever-changing threat landscape. AlienApps enable security orchestration and automation capabilities with both third-party technologies and within the platform itself, which are needed to properly coordinate an effective response to the latest threats. This is the power and promise of AlienApps.
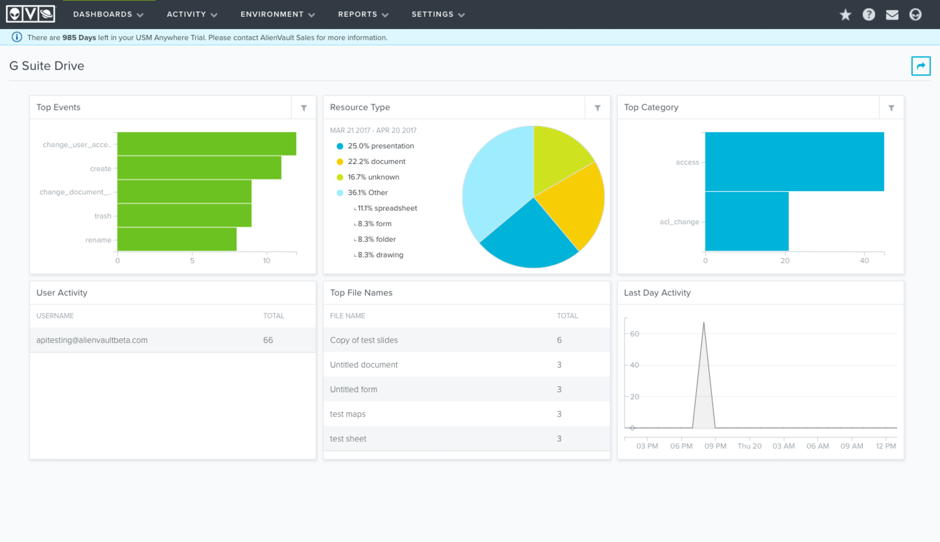
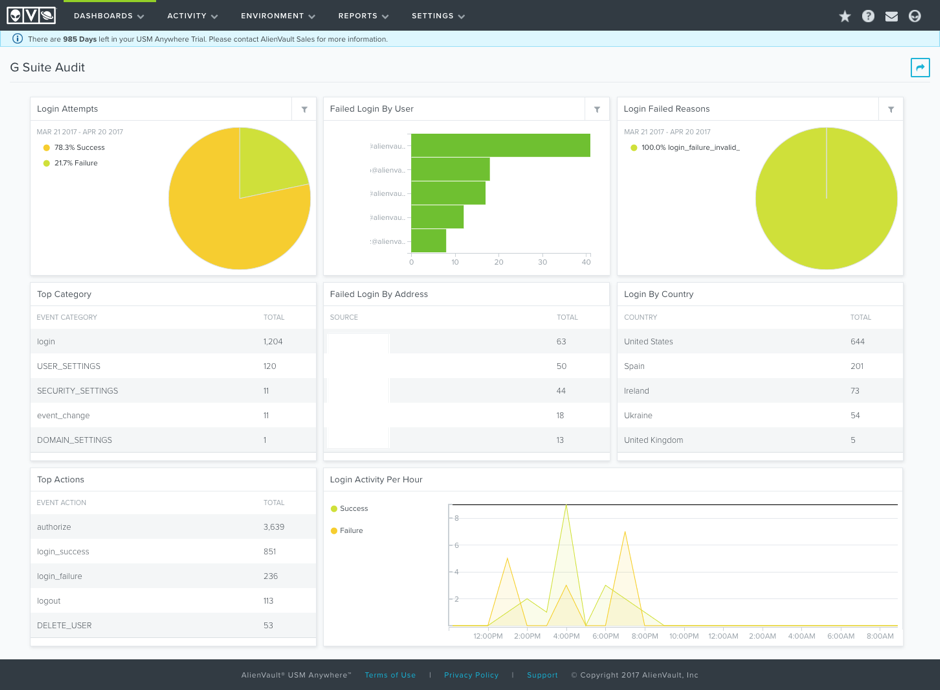
The AlienApp for G Suite was recently made available to provide organizations with comprehensive visibility into all user and administrative activity within G Suite. Prebuilt, interactive dashboards provide an at-a-glance view into the user activity and help you quickly discern potential security risks.
AlienVault can be quickly and easily hooked into G Suite, leveraging the same OAuth functionality used by the threat actor described in this blog to connect and collect the activity directly from the G Suite API. This provides USM Anywhere with the data and context to understand what users are doing, what documents they are sharing, and what applications are being authorized via OAuth.
As you can imagine, this is very valuable from a forensic point of view. This allows you to:
- Validate if any of your users were affected by the malicious application
- Generate alerts based on application activity
- Report and hunt on different applications that your users have connected to their corporate accounts.
Finally, we have included a default correlation rule in USM Anywhere that will alert when a user authorizes an application with dangerous permissions, such as access to email and contacts.
USM Anywhere, combined with the AlienApp for G Suite (included out of the box with USM Anywhere at no additional cost) provides the information that even the most under-resourced IT security teams need to effectively monitor their G Suite environments for potential threats and compromise.