The LevelBlue USM Central web user interface (UI) provides access to your connected deployment Entire process involved in installation, configuration, startup, and testing of hardware and software in a specific environment. so you can manage its security. From the USM Central web UI, you can view all essential information, like alarms Alarms provide notification of an event or sequence of events that require attention or investigation., vulnerabilities A known issue or weakness in a system, procedure, internal control, software package, or hardware that could be used to compromise security., configuration issues An identified configuration of deployed software or features of software that is in use, which is known to be insecure., deployments, system events, system settings, and rules for each deployment. This interface enables you to connect existing deployments or create new ones. You can also create new users in the USM Central instance.
Note: The recommended screen resolution for viewing the USM Central web UI is 1440 pixels wide.
For the USM Central web UI to load successfully, it needs to access some external URLs in addition to the one reserved for the USM Central instance. If your company operates in a highly secure environment, you must change permissions on your firewall for USM Central to gain access. The following table summarizes the URLs that the USM Central web UI uses.
The following table shows the URLs used by USM Central.
| URL | Ports |
Purpose |
|---|---|---|
| <your USM Central subdomain>.alienvault.cloud | 443 | USM Central ongoing communication |
| api-iam.intercom.io | 443 | USM Central in-product announcements |
| cdn.amplitude.com | 8080 | USM Central telemetry data collection |
| events.split.io | 443 | USM Central feature flags |
| sdk.split.io | 8080 | USM Central feature flags |
| www.google-analytics.com | 443 | USM Central website traffic analysis |
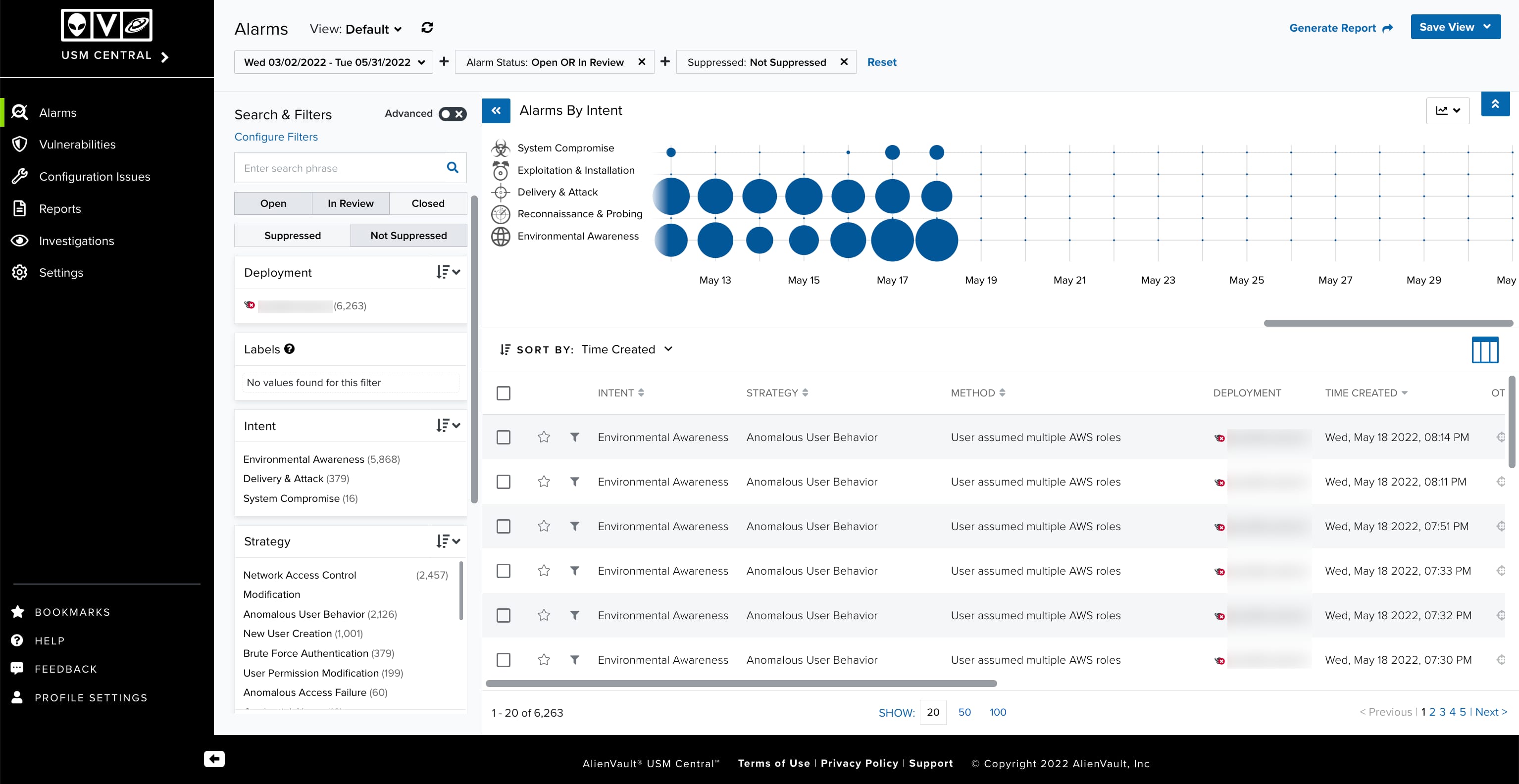
The USM Central web UI runs in any standard web browsers. When you first log in, it displays the Alarms main page.
The main navigable elements and expand selections are provided consistently through the web UI. Use the and
icons to expand or collapse the left navigation pane.
Important: You can also load the default landing page by clicking the logo of USM Central located in the upper-left corner of the page.
The primary menu provides access to the main functions or operations of USM Central. These include the following:
- USM Central: Displays a list of connected deployments. Select a deployment in the list to open the console for the deployment in another browser tab or page.
- Alarms: Displays alarms and enables the search, sorting, filtered selection, and visualization of the alarms. See Alarms Management for more information.
- Vulnerabilities: Displays vulnerabilities display and enables the management of the vulnerabilities. See Vulnerabilities for more information.
- Configuration Issues: Displays configuration issues and enables the management of the configuration issues. See Configuration Issues for more information.
- Reports: Displays reports that result from the export data that you c an find in alarms, vulnerabilities, and configuration issues, and enables the management of the reports. You can also choose the format of the report (PDF and CSV). See Saved Reports for more information.
- Settings: Provides access options to view and manage connected deployments. This option also enables you to manage users, system events, orchestration rules, and set a session timeout. See View Deployments, User Management, System Events Management, Orchestration Rules Management, and Configuring Web UI Session Timeout for more information.
Note: Either the admin IP address or the virtual private network (VPN) endpoint IP address must be routable from the browser for the link to work.
The secondary menu provides access to the system configuration, the user profile information, the help link, and the bookmarked items:
- Bookmarks: The
icon enables you to see and access alarms, vulnerabilities, and configuration issues that you bookmarked for easy access. The number on the icon indicates the number of items bookmarked.
- Help: The
icon includes these options:
- Documentation: Links to online documentation.
- Support: Links to the LevelBlue Support page.
- Feedback: The
icon provides direct line of communication with the USM Anywhere team.
- Profile Settings: The
icon includes these options:
- Profile: Opens the profile settings page where you can change your full name, update your password, enable multi-factor authentication (MFA A method of access control in which a user is granted access only after successfully presenting several separate pieces of evidence to an authentication mechanism – typically at least two of the following categories: knowledge, possession, and inherence.) for the account, configure an interval for auto-refreshing the alarms page. See Using Multi-Factor Authentication and Managing Your Profile Settings for more information.
- API Clients: Opens the API Clients on the profile settings page. See API Clients for more information.
- Logout: This option logout the user.
 Related Video Content
Related Video Content Feedback
Feedback