 Role Availability Role Availability
|
 Read-Only Read-Only
|
 Investigator Investigator |
 Analyst Analyst
|
 Manager Manager
|
When you sign up for and connect your Open Threat Exchange® (OTX) The world’s first truly open threat intelligence community that enables collaborative defense with actionable, community-powered threat data. This repository provides a continuous view of real time malicious activity. account to your USM Anywhere deployment Entire process involved in installation, configuration, startup, and testing of hardware and software in a specific environment., it configures USM Anywhere to receive raw pulse data and other IP reputation Threat ranking of IP addresses that have been submitted by the OTX community as being malicious or at least suspicious. information. (Reputation data is updated separately from OTX pulse OTX pulses provide information on the reliability of threat data, who reported a threat, and other details of threat investigations. information.)
USM Anywhere then correlates that data with incoming events Any traffic or data exchange detected by LevelBlue products through a sensor or external devices such as a firewall., alerting you to OTX pulse and IP Reputation-related security events Information collected and displayed that describes a single system or user level activity that took place. and alarms Alarms provide notification of an event or sequence of events that require attention or investigation. when it detects IOCs Indicator of Compromise interacting with assets An IP-addressable host, including but not limited to network devices, virtual servers, and physical servers. in your environment. Such interactions might consist of malicious Activity in a system that exceeds or misuses that access in a manner that negatively affects the confidentiality, integrity, or availability of the organization's information systems. IPs communicating with systems, malware Generic term for a number of different types of malicious code including viruses, worms, and Trojans. detected in your network, or outbound communication with command-and-control (C&C) servers.
Connecting OTX to USM Anywhere helps manage risks and threats in these ways:
- USM Anywhere receives threat updates every 15 minutes in the form of raw data for all pulses to which you subscribe, either directly or through subscriptions to other OTX users.
- You receive updates on your subscribed pulses by email, either individually as they occur or in digest mode.
- You can review an OTX pulse activity feed containing detailed analytics about related threat vectors reported by OTX.
- As soon as you log into Log in (verb): Process in which an individual gains access to a computer system after providing sufficient credentials to authenticate their unique identity. Login (noun): User credentials, typically a username and matching password. USM Anywhere, you can see which pulses are most active in your environment by looking at Open Threat Exchange Dashboard.
- USM Anywhere evaluates IOCs against all events as long as they are generated and generates an alarm when a malicious IP address communicates with any of your assets, or when any other IOCs become active in your network.
OTX Account and OTX Key
USM Anywhere enables you to display OTX information if you have a valid OTX key. Go to Settings > OTX to see the LevelBlue Open Threat Exchange (OTX) page.
See Entering Your OTX Key for more information about how to enter your OTX key.
OTX IP Reputation Data Correlated with Events
USM Anywhere maintains an IP reputation list that stores data it receives from OTX about public IP addresses involved in malicious or other suspect activities. Whenever an event has its source or destination IP Target IP address for an event. addresses listed in the IP Reputation list, reputation data will be added to the data stored for the event. This enables USM Anywhere to support some additional features like re-prioritization of events and alarms depending on the IP of the hosts Reference to a computer on a network. involved.
The IP reputation list maintained by USM Anywhere is stored on the USM Anywhere Cloud The use of many computers connected over a network to run multiple programs or applications at the same time, instead of running them on a local device or network.. Activity, Reliability, and Priority values provided by OTX are saved with event information for those events having reputation data for either source or destination IP addresses.
The main purpose of the IP reputation list is to provide a list of known or potentially dangerous IP addresses. If any alarm or event is generated by the action of a listed dangerous IP address, then this event will have a smaller probability of being a false positive A condition that is flagged as a vulnerability or weakness that is not actually a concern. This may be caused by other mitigating conditions (such as additional security technology) or inefficient tuning of detection technology.. This also enables for the recalculation of event/alarm risk depending on its "IP Reliability" and "IP Priority" values.
Note: Reputation events are anonymized and submitted to the LevelBlue OTX service for those customers who enable that capability in USM Anywhere. With the feedback received from customer systems and all the other sources LevelBlue uses, the IP Reputation values are updated before being redistributed to customers.
Displaying Alarms and Events Based on OTX Pulse and IP Reputation
The USM Anywhere Alarm and Events web UI provides methods of searching for and filtering alarm and security events based on OTX pulse and IP Reputation information. For each event, the database stores associated information on the source and destination IP address provided by OTX, in addition to the activity reported in the event, for example, spamming, phishing Use of emails that appear to originate from a trusted source to trick a user. Emails usually contain links to external websites designed to trick users into entering valid credentials or contain malware in an attachment designed to allow the attacker remote access., scanning, malware distribution, and so on.
Searching, Filtering, and Viewing Alarms
Different from the way other alarms are processed, USM Anywhere generates an alarm whenever it detects even one event associated with an OTX pulse. Alarm correlation Correlation identifies potential security threats by identifying relationships between multiple types of events occurring in two or more assets. begins at that point and proceeds for a period of 24 hours. During this time, USM Anywhere adds any new events related to that pulse to the same alarm.
If any new events related to the pulse occur after that 24-hour period, USM Anywhere generates a second alarm and a new correlation period begins. As an exception to this rule, should an event contain data on record with OTX IP Reputation information, USM Anywhere correlates the alarm, using its standard directive taxonomy Taxonomy is a classification system for security events. LevelBlue open source security event taxonomy is a classification system based on 20 main categories and 240 subcategories..
Note: If an OTX pulse is creating too much noise and generating too many false positive alarms, you can always just unsubscribe from the pulse.
USM Anywhere does not offer a filter for IP Reputation-based alarms. However, you can view these within the Alarms list, where they occur. See Alarms List View for more information.
You can configure the columns/fields related to OTX information to be displayed in the list and save your columns configuration to get back to it whenever you need it. See Configuring Columns within List View for more information.
Important: The "Suspicious Behavior - OTX Indicators of Compromise" correlation rule generates alarms if the pulse comes from the LevelBlue OTX account.
Searching, Filtering, and Viewing Events
From the USM Anywhere Events main page, you can search for and filter events based on whether OTX pulses exist for source or destination IP addresses, as well as the severity of different IP Reputation scores. See Events List View for more information.
This screenshot displays the search and filter OTX options:
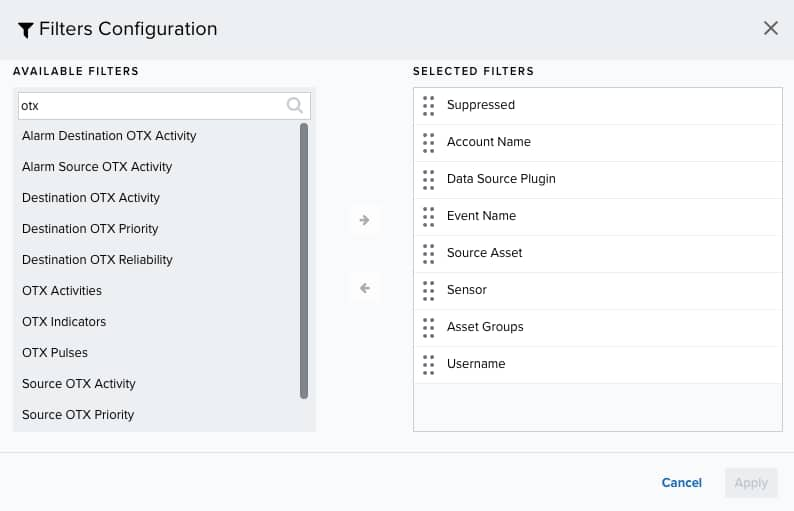
You can configure the columns and fields related to OTX information to be displayed in the list and save your columns configuration to get back to it whenever you need it. See Configuring Columns for more information.
Once you have made your selection, the Event list display will be updated to show only those events matching the IP Reputation criteria you specified, plus OTX pulse information, if you selected that option.
In the Events main page, you can click the icon to display the OTX IP Reputation information available for an event. This icon opens the LevelBlue OTX page.
Creating rules using OTX and Threat Intelligence IOC fields
USM Anywhere enables you to create orchestration rules using OTX and threat intelligence Indicator of Compromise (IOC) fields and functions. You can select the OTX and threat intelligence fields as conditions to create an orchestration rule. See Orchestration Rules for more information and this example of how to create an alarm rule using threat intelligence IOC fields.
To create an alarm rule using threat intelligence IOC fields
- Go to Settings > Rules > Orchestration Rule.
- Select Create Orchestration Rule > Alarm Rules.
- Click Add Condition and select the property values you want to include in the rule to create a matching condition.
-
(Optional.) Click Add Group to group your conditions.
Note: See Operators in the Orchestration Rules for more information.
-
In the Occurrences text box, enter the number of event occurrences that you want to produce a match on the conditional expression to trigger the rule.
You can enter the number of occurrences or use the arrows to scroll the value up or down. You can enter a number between 1 and 100.
- Click Next.
- Enter a name for the rule.
- Select an intent.
- Enter a method.
- Select a strategy.
- Enter a priority.
- Configure a mute duration set in seconds, minutes, and hours.
-
In the Length text box, specify the timespan that you want to use to identify a match for multiple occurrences. Enter the number in the text box, and then use the drop-down menu to select a value of seconds, minutes, or hours.
This duration identifies the amount of time that transpires from the beginning to the end of the occurrence. If the number of occurrences is not met within this period, the rule is not a match.
-
Select the fields that you want to display in the generated alarm.
You can select or remove the fields you want to include in the details of the alarm by clicking the
and the
icons.
- Click Save
Note: If the field is related to the name of a country, you should use the country code defined by the ISO 3166.
Note: The Sources or Destinations field needs to match the universally unique identifier (UUID) of the event or alarm. You can use the Source Name or Destination Name field instead.
Important: Instead of using the equals and equals, case insensitive operators for array fields, LevelBlue recommends the use of the in or contains operators.
Note: If you need to add a property value that maps with a property key, you need to know the mapping of the field. See Determining the Mapping of a Field for more information.
The intent describes the context of the behavior that is being observed. These intents roughly map to the stages of the intrusion kill chains but are collapsed to ensure that each is discrete. See Intent for more information about the available threat categories.
If known, it is the method of attack or infiltration Indicator that specifies the method of attack that generated an alarm. For Open Threat Exchange® (OTX™) pulses, this method is the pulse name. associated with the indicator that generated the alarm.
Note: This is a required field; if you do not complete this field, the Save button remains inactive.
The strategy describes the broad-based strategy or behavior that is detected. The intention is to describe the malicious Activity in a system that exceeds or misuses that access in a manner that negatively affects the confidentiality, integrity, or availability of the organization's information systems. user's strategy to achieve their goal.
See Priority Field for Alarms for more information.
You can use the mute value to set the period of time during which, once an alarm is createdUSM Anywhere will not create a new alarm based on the same conditions.
Note: Take care to set a mute duration that is long enough to cover the span of time in which matching events will occur to maximize the efficacy of your mute.
Important: If your USM Anywhere™ is restarted when one of your alarm mutes is active, or if there is an update or hotfix, the alarm mute will be canceled.
Note: Your defined length and occurrences function together to specify the number of occurrences within a time period that will produce a match for the rule. For example, you can define a rule to trigger an alarm Alarms provide notification of an event or sequence of events that require attention or investigation. for an unauthorized access An incident-type categorization that may be a precursor to other actions or stages of an attack. attempt when a failed SSH Program to securely log into another computer over a network, execute commands in a remote machine, and move files from one machine to another through Secure Copy (SCP). login Log in (verb): Process in which an individual gains access to a computer system after providing sufficient credentials to authenticate their unique identity. Login (noun): User credentials, typically a username and matching password. occurs three times within a five-minute window.
The created rule displays in the list of rules. See Alarm Rules from the Orchestration Rules Page for more information.
 Feedback
Feedback