 Role Availability Role Availability
|
 Read-Only Read-Only
|
 Investigator Investigator |
 Analyst Analyst
|
 Manager Manager
|
USM Anywhere enables you to easily identify existing and emerging threats, which are of interest. Through alarm Alarms provide notification of an event or sequence of events that require attention or investigation. rules on events Any traffic or data exchange detected by LevelBlue products through a sensor or external devices such as a firewall., you can organize your threats and only see high-priority alarms, which can be received in an email and will help you to reduce noise and focus on important things.
To create an alarm rule from the Events page
- Go to Activity > Events.
-
Search the events which you want to include in the alarm rule.
See Searching Events for more information.
- Click one of them.
- Select Create Rule > Create Alarm Rule.
-
Select a Boolean operator.
The options are AND, OR, AND NOT, and OR NOT.
-
Select a packet type in the Match drop-down list.
- Logs: Use this packet type for event-based rules.
- Configuration Issues: Use this packet type for configuration issues-based rules1.
- Vulnerabilities: Use this packet type for vulnerabilities-based rules.
- System Events: Use this packet type for system events-based rules.
- Console User Events: Use this packet type for console user events-based rules.
- You have already suggested property values to create a matching condition. If you want to add new property values, click Add Condition.
-
(Optional.) Click Add Group to group your conditions.
Note: See Operators in the Orchestration Rules for more information.
-
In the Occurrences text box, enter the number of event occurrences that you want to produce a match on the conditional expression to trigger the rule.
You can enter the number of occurrences or use the arrows to scroll the value up or down. You can enter a number between 1 and 100.
- Click Next.
- Enter a name for the rule and, if desired, a description to clarify its use in the Description field.
- Select an intent.
- Enter a method.
- Select a strategy.
- Enter a priority.
- Configure a mute duration set in seconds, minutes, and hours.
-
In the Length text box, specify the timespan that you want to use to identify a match for multiple occurrences. Enter the number in the text box, and then use the drop-down menu to select a value of seconds, minutes, or hours.
This duration identifies the amount of time that transpires from the beginning to the end of the occurrence. If the number of occurrences is not met within this period, the rule is not a match.
-
(Optional.) Select the fields that you want to display in the generated alarm.
You can select or remove the fields you want to include in the details of the alarm. A field passes from one column to the other by clicking it.
-
Click Save.
The created rule displays in the list of rules. You can see it from Settings > Rules. See Orchestration Rules for more information.
Note: Less common parameters will appear as paired Custom Header N and Custom Field N rows with the parameter's name and value. N represents the number that is automatically given to the parameter.
Note: If the field is related to the name of a country, you should use the country code defined by the ISO 3166.
Note: The Sources or Destinations field needs to match the universally unique identifier (UUID) of the event or alarm. You can use the Source Name or Destination Name field instead.
Important: Instead of using the equals and equals, case insensitive operators for array fields, LevelBlue recommends the use of the in or contains operators.
Note: If you need to add a property value that maps with a property key, you need to know the mapping of the field. See Determining the Mapping of a Field for more information.
Note: The current rule box shows you the syntax of your rule, and the rule verification box reviews that syntax before saving the rule.
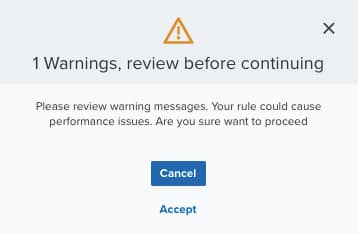
Important: A dialog box opens if there are warning messages. Click Cancel to review the warning messages, or click Accept to continue creating the rule.
The intent describes the context of the behavior that is being observed. These intents roughly map to the stages of the intrusion kill chains but are collapsed to ensure that each is discrete. See Intent for more information about the available threat categories.
If known, it is the method of attack or infiltration Indicator that specifies the method of attack that generated an alarm. For Open Threat Exchange® (OTX™) pulses, this method is the pulse name. associated with the indicator that generated the alarm.
Note: This is a required field; if you do not complete this field, the Save button remains inactive.
The strategy describes the broad-based strategy or behavior that is detected. The intention is to describe the malicious Activity in a system that exceeds or misuses that access in a manner that negatively affects the confidentiality, integrity, or availability of the organization's information systems. user's strategy to achieve their goal.
See Priority Field for Alarms for more information.
You can use the mute value to set the period of time during which, once an alarm is createdUSM Anywhere will not create a new alarm based on the same conditions.
Note: Take care to set a mute duration that is long enough to cover the span of time in which matching events will occur to maximize the efficacy of your mute.
Important: If your USM Anywhere™ is restarted when one of your alarm mutes is active, or if there is an update or hotfix, the alarm mute will be canceled.
Note: Your defined length and occurrences function together to specify the number of occurrences within a time period that will produce a match for the rule. For example, you can define a rule to trigger an alarm Alarms provide notification of an event or sequence of events that require attention or investigation. for an unauthorized access An incident-type categorization that may be a precursor to other actions or stages of an attack. attempt when a failed SSH Program to securely log into another computer over a network, execute commands in a remote machine, and move files from one machine to another through Secure Copy (SCP). login Log in (verb): Process in which an individual gains access to a computer system after providing sufficient credentials to authenticate their unique identity. Login (noun): User credentials, typically a username and matching password. occurs three times within a five-minute window.
Important: It takes a few minutes for an orchestration rule to become active.

 Feedback
Feedback