 Role Availability Role Availability
|
 Read-Only Read-Only
|
 Investigator Investigator |
 Analyst Analyst
|
 Manager Manager
|
The BlueApp for SpyCloud Dark Web Monitoring monitors reports that breach records of compromised emails from that domain or assetsassociated with it. You can use this information to identify employees and consumers that have malware infections and protect yourself from potential fraud.
Malware often captures user credential information, such as usernames and passwords, along with other information and stores the stolen information on command and control (C2) servers. In cases where SpyCloud has recovered C2 data, it will analyze the records and classify them as either infected employee records or infected customer records.
For example, if one of the monitored domains is "example.com," then emails addressed from "[name]@example.com" that indicate a breach would be classified as an "employee" record. If the malware came from an unmonitored external domain, it is then classified as a "customer" record.
See the guide on infected users for more information.
The following table lists the fields available for SpyCloud events.
| Field | Description |
|---|---|
| Source DNS Domain | Domain name associated with the breach record. |
| Event Ref Date | The date on which the record entered the SpyCloud systems, in ISO 8601 date-time format. |
| Source Username | Username associated with the breach record. |
| Source User Email |
The email address associated with the breach record. |
| Public Breach | A true/false flag that indicates if the breach has been disclosed to the public. |
| Infected User | A true/false flag that indicates if the credentials were obtained by a keylogger. |
|
Source ID |
SpyCloud-generated numerical identifier for the breach in which the credentials were found. |
| Password Type | The password type identified in the breach record. |
| IP Addresses |
List of one or more IP addresses in alphanumeric format (both IPV4 and IPv6 addresses are supported). |
|
Sighting |
(SpyCloud subscriptions only) An integer that indicates the occurrence of a breached credential across the entire SpyCloud breach catalog A value of “3” would indicate that this breach record is the third occurrence of the credential in the catalog. |
Note: The BlueApp for SpyCloud Dark Web Monitoring leverages the SpyCloud APIs to retrieve breach records. See the SpyCloud API documentation for more information about the attributes (data fields) it stores in these breach records.
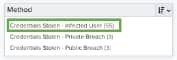
USM Anywhere generates an alarm from one or more of these events using built-in correlation rules, which analyze the events for patterns that indicate a new breach that requires attention and investigation. It generates the alarm as a Security Critical Event with the following assessed breach method:
- Credentials Stolen — Public Breach
- Credentials Stolen — Private Breach
- Credentials Stolen — Infected User
Additional parameters of a generated alarm are determined by the information in the associated events. For example, an alarm will provide different guidance if an event indicates that the compromised credential is from an infected user, because a simple password reset would be an ineffective response in that situation.
- Go to Activity > Events to open the Events page.
-
If the Search & Filters panel is not displayed, click the
icon to expand it.
USM Anywhere includes several filters displayed by default.
-
(Optional.) Scroll down to the Data Source filter and select SpyCloud to display only the Dark Web Monitoring events on the page.
If this filter is not displayed, click the Configure filters link, which is in the upper left corner of the page, to configure filters for the page. See Managing Filters for more information about configuring filters for pages.
-
Select an event in the list to view detailed information.
- Go to Activity > Alarms to open the Alarms page.
-
If the Search & Filters panel is not displayed, click the
icon to expand it.
USM Anywhere includes several filters displayed by default.
-
Enter SpyCloud as a search phrase and click the
icon.
-
(Optional.) Scroll down to the Method filter and select a type to view only those alarms.
If this filter is not displayed, click the Configure filters link, which is in the upper left corner of the page, to configure filters for the page. See Managing Filters for more information about configuring filters for pages.
-
Select an alarm in the list to view detailed information and recommendations.




 Feedback
Feedback