| Applies to Product: |
|
|
After USM Appliance is installed in your environment, events start flowing through the USM Appliance system, so you can start gaining visibility into what natural or non-threatening activity is taking place, and what worrisome activity, indicating possible attacks, might be taking place. USM Appliance also begins collecting other information about your network and various network devices such as firewalls, routers and switches, servers, and applications. In addition, it is discovering and determining possible vulnerabilities and threats your environment might be susceptible to.
The following illustration details a high level view of events and other information from your network environment as it is collected or generated by USM Appliance Sensors and delivered to the USM Appliance Server for processing.
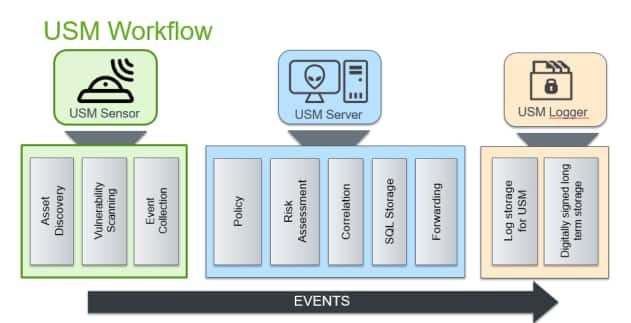
The USM Appliance Sensor combines asset discovery, vulnerability assessment, threat detection, and behavioral monitoring to provide full situational awareness. The USM Appliance Sensor is the front-line security module of the USM Appliance platform and provides detailed visibility into your environment, vulnerabilities, attack targets and vectors, and services.
The USM Appliance Sensor normalizes raw log data and other activity or status information from devices into a standardized USM Appliance event format. These normalized events are then sent to the USM Appliance Server component.
The USM Appliance Server provides a unified management interface through the USM Appliance web UI that combines security automation, and OTX and LevelBlue Labs™ Threat Intelligence to correlate data, spot anomalies, reduce risk, and improve operational efficiency.
The USM Appliance Server receives events from the USM Appliance Sensor and performs policy evaluation. The policy defines what will happen with events. By default, the events are sent to the correlation engine, from the risk assessment module, and then stored in an internal SQL database. Events can also be forwarded to another USM Appliance Server, if required. This flow is completely configurable using USM Appliance policies.
Correlation can be done logically, where events can be compared to patterns and multiple conditions can be connected by using logical operators such as OR and AND. Correlation can also be calculated using cross-correlation, where events are correlated with vulnerability data. After events are processed and correlated, the USM Appliance Server performs risk analyses and triggers an alarm if the risk of the event is high enough.
The USM Appliance Logger is the secure data archival component of the USM Appliance platform. It stores a copy of all USM Appliance event data that can be used for compliance reporting, or retrieved for later forensics and investigation of past incidents.
 Feedback
Feedback